During our recent three day Third-Party Risk Management Bootcamp, we had a lot of GREAT questions come in. It was quite impossible to get to them all during the live sessions, so we have worked with our speakers to compile the answers. Below you will find answers to questions posed during Day 3 - Session 2: Dissecting a Vendor SOC Audit Report.
Day 3 – Session 2
Dissecting a Vendor SOC Audit Report
 |
 |
| Mike Morris Partner PKM |
Mary Beth Marchione Systems Senior Manager PKM |
This session was led by Mike Morris and Mary Beth Marchione at PKM where they discussed the vendor SOC audit report in detail. They have kindly provided answers to the following questions.
Q1: SOC reports that we typically receive are completed holistically for the vendor and all of their clients. At times, the work they do for us is not included. How relevant would that SOC report be to us?
Answer: “They should have a report (or reports) that cover all of their critical services. It might be that they are just providing the wrong report. If your service is omitted, ensure that you contact the vendor to request that they include the scope in the next report. In the meantime, see if you have a ‘right to audit’ clause in your contract that can allow you to audit their services that have been omitted.”
Q2: You mentioned having various control teams reviewing SOC 1s. Should business unit experts also be involved to ensure the areas that are at risk for the activities outsourced are covered in the report?
Answer: “Ideally, yes, business unit experts should be reviewing the reports to ensure that they’re covering the correct services.”
Q3: What is a SOC 3 Report?
Answer: “A SOC 3 is a general use report. It’s an attestation (the auditor provides an opinion) on the chosen Trust Services Criteria: Security, Availability, Confidentiality, Processing Integrity, and/or Privacy. This report provides only the auditor’s opinion if the entity maintained an effective control system. It doesn’t include details. It’s basically a boiled down SOC 2.”
Q4: How does the vendor’s use of Cloud services (i.e. AWS) factor into the SOC reporting?
Answer: “Cloud providers are typically carved out of your vendor SOC reports. In most instances, we find that institutions are able to obtain the cloud provider’s SOC reports as well.”
Q5: Is there a special report or control objective for cloud computing?
Answer: “No. Cloud computing providers typically obtain SOC 2 reports.”
Q6: The SOC 2 report I just received from a critical vendor looks exactly like your SOC 1 sample and only indicated a point in time and not a period. The sections are less extensive than your sample for SOC 2 as well. However, the footer on each page states SOC 2.
Answer: “To clarify, a SOC 1 is a report over internal controls over financial reporting that includes evaluation of management’s control objectives. A SOC 2 report is a report that includes evaluation of the chosen AICPA Trust Services Criteria (Security, Availability, Confidentiality, Processing Integrity, and/or Privacy). Both a SOC 1 and SOC 2 report can be a Type 1 or a Type 2. In a Type 1 the auditor evaluates the design of controls as of a point in time. In a Type 2 report the auditor evaluates the design of controls and if they have operated effectively over a period of time.
If the controls you expect to be included are missing from the SOC 2 report, there could be confusion on the vendor or the service auditor’s part. I would investigate this further to see where the disconnect it.”
Q7: Is it normal/acceptable to require both a SOC 1 and SOC 2 from a vendor?
Answer: “We are seeing more institutions requiring both. It really depends on the nature of the services provided by your vendor. If there’s a direct financial impact, then a SOC 1 is appropriate. If not, then a SOC 2 is appropriate. In some cases where your vendor is handling sensitive information in addition to having a direct financial impact, a SOC 1 may not cover the breadth of controls necessary around security, availability, confidentiality, etc.”
Q8: Is it a written assertion that a vendor is adhering to their subservice Complimentary User Entity Controls vs. written assertion?
Answer: “The bottom line is that your vendor should be adhering to the CUECs of the subservice organization(s). Receiving a written assertion from management specifically stating this is a good way to start. In addition, you may want to ask for their vendor review/due diligence package. That would contain the supporting evidence and may include more detail as to how your vendor evaluates the CUECs of its subservice organizations.”
Q9: If there’s a deficiency like the 24-hour example, should there be a follow-up test after a certain period to ensure the controls are actually in place?
Answer: “Some vendors will have deficiencies retested, but typically you have to wait until the next SOC report is issued to determine whether a deficiency has been remediated. If you have a “Right to Audit” clause, you should be able to go in and review the vendor’s remediation efforts.”
Q10: What is the source of the Complimentary User Entity Controls, which the independent auditor may include in a SOC report?
Answer: “It’s specifically tied to controls that your organization is responsible for, ensuring that the internal control environment between you and the vendor is complete. If you’re not compliant with a CUEC, there is a control gap that your organization is responsible for. CUECs are specific to the unique service that is being provided and are related to the control objectives/criteria and controls in the report.”
Q11: Should we be asking for security documents for more than just the current reports?
Answer: “It depends what is provided. If there is missing documentation, then you should request additional security documentation. If the vendor is processing material transactions and/or houses non-public customer information, you should be receiving documents of the vendor’s cyber resilience, if they are not directly referenced in the vendor’s SOC report.”
Q12: What types of procedures do you recommend be done if you can't get a SOC report from a subservice?
Answer: “If the contractual relationship allows, you should be performing due diligence on the subservice providers as well. However, you should be obtaining and reviewing your vendor’s vendor management program and determine if it covers the elements that are required by the FFIEC and whether it is performed annually.”
Q13: What dictates or triggers the need to request and review a SOC report for a subservice third party/fourth party?
Answer: “You need to determine whether the subservice organization poses significant risk to you and/or your customers. The nature of the subservice’s responsibilities should be detailed in the SOC report. If your non-public customer information is sent to the subservice provider, then your GLBA risk will extend to the subservice organization. You should also refer to guidelines in your vendor management program to determine the risk/tier that vendor may be as it relates to your organization.”
Q14: What would be the longest length of time you would accept a gap letter to cover?
Answer: “Bridge letters serve the purpose of providing information from the service organization about their control environment during a period of time in between annual audit reports. The service organization can provide a bridge letter that covers the “gap” between the report date and another date such as the end of the fiscal year, for example. This is generally given from service organization to cover several months, but not an extended period of time (18 months). Within an 18-month period, the service organization should have had an audit.”
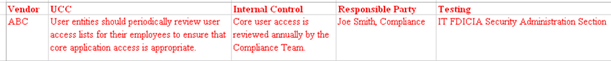
Q15: For control considerations annual verification how do you document all the different vendor key controls and that they have been validated?
Answer: “To appropriately verify your organization addresses service organization control considerations, key internal controls should be documented by management. In addition, it’s key to note an individual responsible for that portion of the review, and also how that key internal control is tested. Here is an example:
Q16: Have you seen banks request incident response plans and cybersecurity assessments?
Answer: “Yes, many times the incident response plan, a summary of cyber security assessment results, or a summary of penetration testing/network vulnerability assessment results, are included in the unaudited section of the SOC report for reference. Banks do request this information specifically from vendors if it is not included to ensure their incident procedures line up with contractual requirements. We have also seen many Banks request third party assessment results to ensure they are monitoring and remediating any high-risk issues.”
So, you know what a SOC report is and the different types. But do you know what to do with them once you receive them from a vendor? We can help - download our helpful infographic.
Infographic
Donec nec justo eget felis facilisis fermentum. Aliquam porttitor mauris sit amet orci.

Related Posts
Auditor's Perspective on Third-Party Risk Management Q&A
During our recent three day Third-Party Risk Management Bootcamp, we had a lot of GREAT questions...
Third Party Risk Q&A: Vendor SOC Report Types and More
During our recent three day Vendor Management Bootcamp (click here to watch on-demand), we had a...
What to Include In a Third-Party Risk Board Report Package
In the past, we covered that the board needs to be involved in your vendor management program and...
Subscribe to Venminder
Get expert insights straight to your inbox.
Ready to Get Started?
Schedule a personalized solution demonstration to see if Venminder is a fit for you.




.gif?width=1920&name=Sample-Graphic-Animation%20(1).gif)