infographic
CIA Information Security Triad and Your Vendors
CPE Credit Eligible
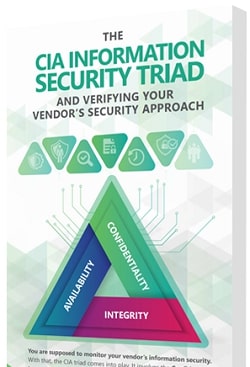
It's a third party risk best practice to monitor your vendor’s information security. With that, the CIA triad comes into play. It involves the Confidentiality, Integrity and Availability of your data.
Download this helpful infographic to learn how your vendor’s approach to Confidentiality, Integrity and Availability impact you and your customers’ data or information.
Download the infographic for:
- What the CIA triad is
- Why you should care
- How to verify your vendor's approach to cybersecurity and information security




.gif?width=1920&name=Sample-Graphic-Animation%20(1).gif)

