When your organization decides to outsource a product or service to a vendor, you might be tempted to think that the most important step is signing the contract. The truth is that negotiating and signing the vendor contract is just one of many important activities you need to perform to properly manage vendor risk. But what exactly are these vendor risk management activities and in which order should they be performed? The vendor risk management lifecycle, or third-party risk management lifecycle, is an easy-to-follow system that organizes these various activities into three distinct phases: onboarding, ongoing, and offboarding.
Let’s review each stage of the vendor risk management lifecycle for a better understanding of how to manage third-party vendor risk.
The Vendor Risk Management Lifecycle
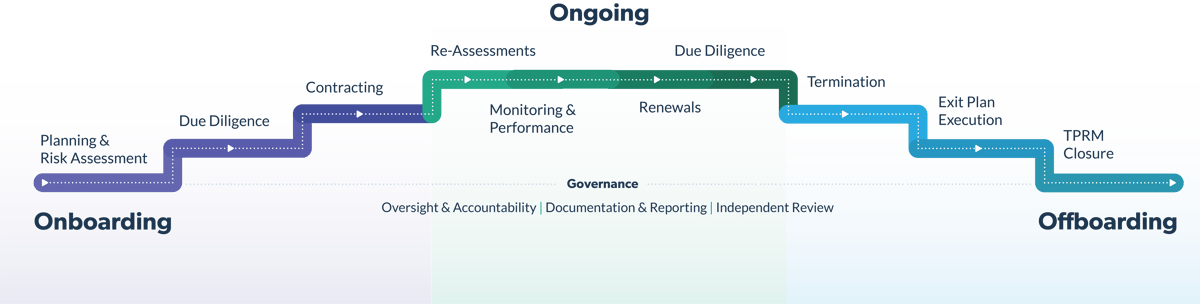
Before diving into each stage of the vendor risk management lifecycle, it’s helpful to recognize three foundational elements known as governance. In the same way that a coach helps guide and support an athlete, lifecycle governance is intended to guide each stage to success. These governance elements include oversight & accountability, documentation & reporting, and independent review. A vendor risk management program built on these foundational elements makes it easier to identify who is responsible for vendor risk management in your organization and how those activities are overseen. It also ensures that you have appropriate documented evidence of vendor risk management processes and activities and provides important information about program compliance and how the overall program can be improved.
The Vendor Risk Management Lifecycle Is Made Up of 3 Main Stages
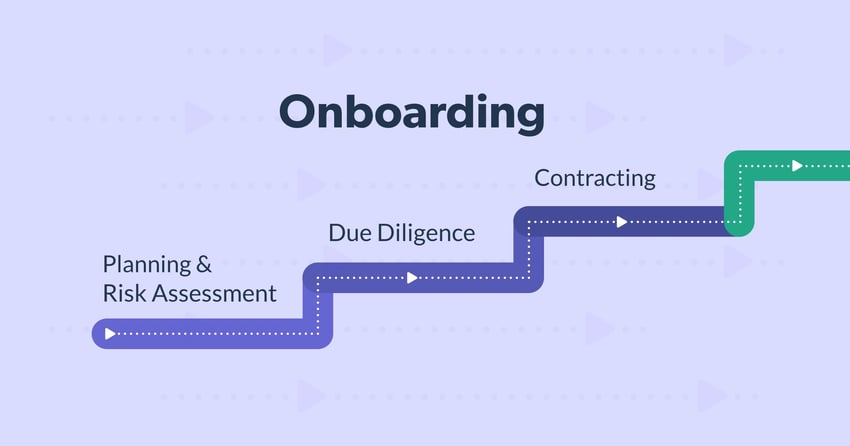
Onboarding Vendors
It may be tempting to rush through the onboarding stage, especially if there’s an immediate need for a vendor’s product or service. However, it’s essential to take a thorough approach to onboarding a vendor, with the following steps:
- Planning & Risk Assessment – Planning for the vendor relationship is an essential first step that includes determining if the product or service is in scope for your program. First, you must decide that the product and service are in your program's scope and determine who will be responsible for the relationship. You must then perform a risk assessment by determining whether that vendor relationship will be critical to your operations, and identify the risks associated with the product or service provided. Inherent risk and criticality are essential factors to understand.
Here's a brief definition of each term:
-
- Criticality - This refers to whether a vendor is essential to your business operation. A critical vendor will significantly impact your organization or customers if its products or services fail to meet your expectations. On the other hand, a non-critical vendor could fail to deliver its products or services without significant impact on your organization or customers.
- Inherent risk - This exists naturally, as part of the vendor's product or service, without considering precautions or controls. Inherent risk is typically measured on a scale of low, moderate, and high.
- Due Diligence – Due diligence is another essential step in vendor onboarding. It enables your organization to confirm that the vendor is a legitimate business in good standing and has the necessary controls. The process involves gathering and validating information about the vendor and then having a subject matter expert review the information and provide a qualified opinion regarding the sufficiency of the vendor's controls. When due diligence is complete, you can calculate the level of residual risk (or the level of risk after applying controls). Ultimately, it's up to your organization to decide whether the residual risk is acceptable and whether it's worth moving forward.
For each potential vendor, you'll want to perform a thorough vetting process which generally includes the following activities:
-
- Reviewing the vendor's financial history through audited financial statements or other financial records.
- Checking for consumer complaints or any other issues that may expose you to reputational risk.
- Running an OFAC check to confirm the vendor isn't on any sanctions list.
- Contracting – Selecting a vendor and proceeding with the contract is the last component of the onboarding stage. It includes planning, drafting, negotiating, approving/executing, and managing the legal document between the vendor and your organization. Your contract should identify service level agreements (SLAs) and document any essential controls. Keep in mind that the contract isn't restricted to the onboarding stage of the vendor risk management. It plays a significant role throughout the entire lifecycle, including contract renewals and termination.
Ongoing Activities of Vendors
Vendor risk and performance can change throughout the relationship, so it's essential to maintain a practice of ongoing monitoring activities. These activities include periodic re-assessments, ongoing monitoring of risk and performance, formal performance management, contract renewals, and periodic due diligence.
Here’s a closer look at each activity:
- Re-Assessments – The vendor owner should review the inherent risk assessment and update if necessary. If there are any changes to the vendor’s risk, the vendor owner must collect the appropriate due diligence documentation. This should occur at least annually for any critical vendor or those with elevated risk.
- Monitoring & Performance – This activity involves regularly monitoring the vendor’s risk and performance, in between formal risk re-assessments.
These practices will help establish a healthy routine of ongoing monitoring and performance reviews:
-
- Establish a monitoring and review schedule based on the inherent risk rating.
- Create a process to track SLAs.
- Report vendor risk to senior management and the board regularly.
- Renewals – It’s essential to stay on top of important dates, including notice periods for contract renewals and expirations. This ensures you have enough time to make changes to your contract, if necessary.
- Due Diligence – Ensure that all due diligence documents are current and accurate. Insurance certificates can expire and business continuity and disaster recovery plans can become obsolete, so it’s essential to collect and review the most current documents.
Offboarding Vendors
The final stage in the vendor risk management lifecycle is offboarding or terminating the contract. Sometimes you’ll need to offboard the vendor proactively, simply because the contract has expired, and you no longer have a need for their products or services. Other times, vendor offboarding is reactive, occurring because of performance issues or unmet SLAs. Whatever the reason, you’ll want to make sure that you have a documented termination process to help the process unfold smoothly.
Here are the specific activities involved in this stage:
- Termination –This is the official notification to the vendor that the contract won't be renewed. Although you might notify the vendor of their termination well before the contract expiration, the vendor engagement won't officially be terminated until the contractual date.
- Exit Plan Execution –The exit plan should be built during the onboarding stage, and should include the details reflecting your exit strategy (replacing the vendor, bringing the activity in-house, ending the product or service, or a combination of the three options). If possible, the plan should be tested to ensure it's viable. The exit plan should also detail both parties' specific roles, responsibilities, and tasks to exit the relationship safely and soundly. Examples include returning or destroying sensitive data and removing vendor access to data, networks, systems applications, and physical facilities.
- TPRM Closure – After completing the exit plan, there may be a few final steps, such as paying any final invoices, updating vendor status in all systems, and archiving relevant vendor material.
Outsourcing products and services to a vendor can provide many benefits. Still, it's essential to maintain a strong vendor risk management program to protect against the risk. Understanding the 3 stages of the vendor risk management lifecycle is a well-tested strategy that helps manage risk throughout your vendor relationships.
Related Posts
Vendor Lifecycle Management: Overview, Mistakes and Tips
The vendor lifecycle is a series of intricate processes that ensures consistent and proper...
10 Best Practices of Successful Vendor Risk Assessments
Assessing vendor risk is an essential practice for organizations to safeguard themselves and their...
How to Mitigate Third-Party Risks
Failing to address your organization’s third-party risks can have serious consequences. Picture...
Subscribe to Venminder
Get expert insights straight to your inbox.
Ready to Get Started?
Schedule a personalized solution demonstration to see if Venminder is a fit for you.




.gif?width=1920&name=Sample-Graphic-Animation%20(1).gif)