Vendor Site Audit
Use vendor site visits when you're unable to do the due diligence you need.
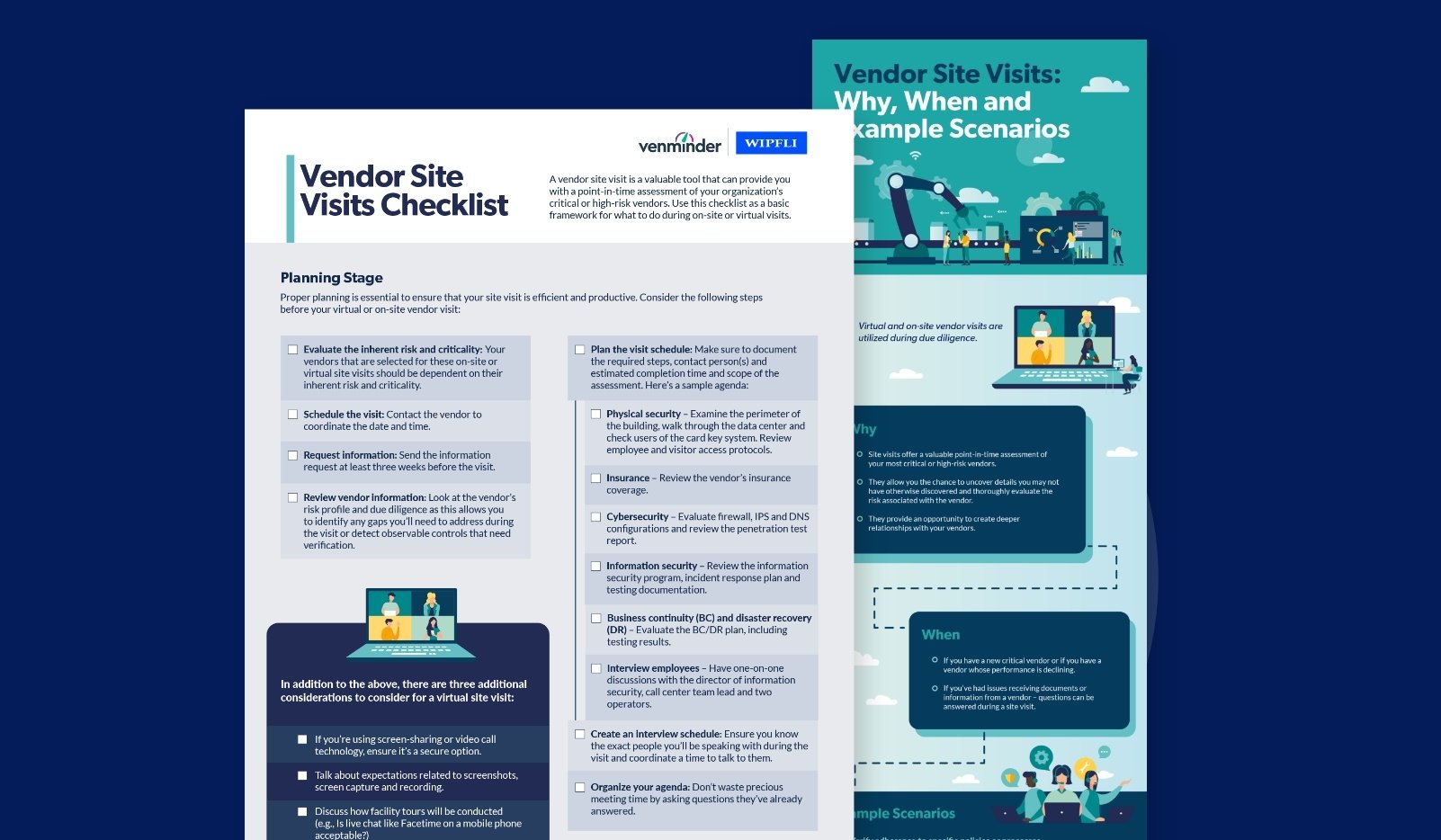
Site visits are critical when a vendor: 1.) doesn’t have proper due diligence documentation to make a risk judgment, 2.) only allows customers to physically view sensitive information on site (such as insurance policies, penetration testing results, business continuity plans, information security policies, etc.) or 3.) has had significant issues identified through their SOC reports or other vendor management documentation.
Venminder has a partner that is proficient in scheduling multiple site visits and performing the site visit audits for you to meet your requirements.
Approach
- Customizing the site visit audit scope/criteria to fit a particular client’s needs
- Breaking the site visits into geographical zones for travel efficiencies
- Creating a project plan to schedule the necessary resources
- Coordinating an on-site interview schedule with the key personnel at the vendor to ensure accessibility and availability
- Conducting site visit wrap up meetings with the vendor’s management team and the client
- Generating reports based upon the approved scope and the findings identified
What It Includes
During a site visit, our team will meet all key vendor personnel, perform physical walkthroughs of the facility, inspect documents (i.e. business continuity plan, incident response policies, penetration testing reports, etc.) and perform audit tests in line with the site visit audit scope/criteria. Any findings identified during our procedures will be communicated to both the client and the vendor’s management team. We will issue a report for each site visit.
The scope of our site visits is customizable by client, and can include, but is not limited to:
- Physical security
- Environmental controls (i.e. power generators, fire suppressions, etc.)
- Business continuity planning
- Cyber resilience (Information security, penetration testing results, incident response planning, etc.)
- Vendor management (how the vendor monitors its vendors)
- Logical security (access to key applications and the network)
- Application change management
- Infrastructure change management
- Risk management
- Insurance coverage
- Management oversight and monitoring
Order Vendor Risk Assessments Online
Assessments can be previewed and ordered directly from the Venminder Exchange

Educational Resources
Ready to Get Started?
Schedule a personalized solution demonstration to see how Venminder can improve your processes.




.gif?width=1920&name=Sample-Graphic-Animation%20(1).gif)