5 min read
CFPB Proposes Major Changes to Small Business Lending Rule (Section 1071)
Here are the latest updates on Section 1071 implementation and broader Consumer Protection Bureau (CFPB) oversight.
...
Browse and search through our free resources created by our in-house experts based on industry guidance and best practices to help you build and improve your third-party risk management program.

Investment advisors outsource to service providers to help run a more efficient practice. But what happens when a service provider harms your business? It’s more common than you think – and the costs of a vendor mistake can be shockingly high.
investement advisor, investments, outsourcing, advisor outsourcing

Understanding how to maximize your TPRM resources will take some effort, but it's a worthwhile goal to help your organization manage risk, regardless of limitations. This informative infographic covers how to maximize your resources.
maximize resources, tprm resources, manage resources, vendor management resources, tprm processes
Keeping your eye on any negative news or adverse media on a third-party vendor is necessary for any organization that wants to safeguard its reputation. Learn examples of adverse media, tips to monitor adverse media, and more.
negative news, reputation risk, vendor reputation, adverse media screening, screening news, safeguard your reputation

By monitoring vendor privacy scores as part of your vendor risk management program, you can mitigate potential risks associated with third parties more effectively. Download this infographic to learn what vendor privacy scores are and more.
privacy scoring, vendor privacy, vendor privacy scores, how to use privacy scores, manage vendor risk, risk mitigation

FINRA has increasingly focused on third-party risk management, outlining its expectations for broker-dealers to manage outsourcing risks. Learn how to comply with these expectations in this eBook
broker-dealer tprm requirements, tprm requirements for broker-dealers, broker-dealers
Financial health is a critical indicator of the vendor’s ability to deliver consistent quality and support when you need it most. That makes vendor financial health an important element to review during your vendor due diligence process. Learn more in the infographic.
poor financial health, poor vendor health, poor vendor financial health, financial health, vendor financial health, struggling vendor
As your vendor inventory grows, so do the challenges; limited resources, increase risk and inconsistent oversight. This infographic share practical tips to help you take control of your large vendor inventory.
vendor inventory, large vendor inventory, vendor inventories, managing vendor inventories, what is a vendor inventory

When outsourcing a product or service to a third-party vendor, your organization is exposed to risks that naturally occur, referred to as inherent risks. Learn sample questions to ask and next steps to take after completing a questionnaire in this eBook.
inherent risk, vendor risk, sample questionnaire, vendor risk assessment, eBook, questionnaire

Download this checklist to ensure your vendor's business continuity and disaster recovery plans are in place and on the right track.
checklist, vendor management, business continuity checklist, vendor business continuity, vendor disaster recover, disaster recovery checklist
What does your fintech company need to know about third-party risk management to meet client expectations and protect your business? Learn more in this infographic
tprm practices, fintech tprm, fintech best practices, best practices for tprm, fintech tprm practices
Do you have some questions about TPRM at your broker-dealer? Learn common questions and answers in this infographic.
small broker-dealers, broker-dealers
Use this checklist as guide for your wealth management firm to manage vendor relationships while maintaining compliance.
wealth management checklist, tprm checklist wealth management, third-party risk for wealth management
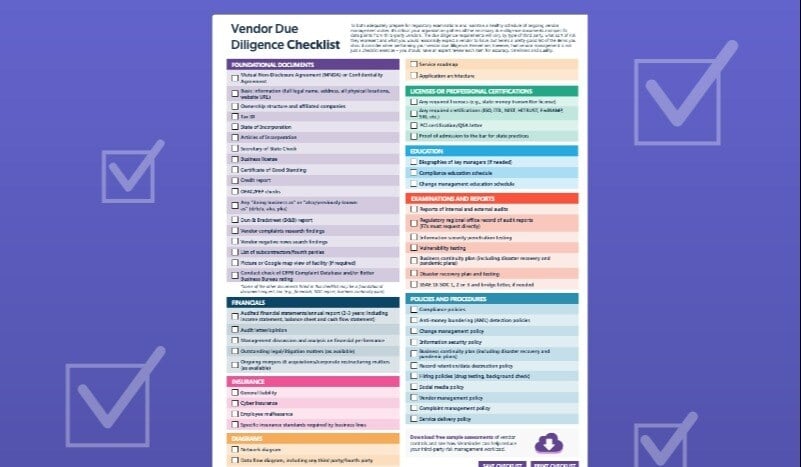
Maintaining a comprehensive checklist ensures you request specific documents that are targeted toward the vendor’s risk level. Use this checklist as a guide.
vendor financial services, financial services due diligence, due diligence for financial services, how to conduct due diligence on financial services
Venminder’s State of Third-Party Risk Management 2025 whitepaper provides third-party risk management insights and industry statistics to help you make informed programs decisions. Learn how others are managing third-party risk.
vendor management, vendor risk management, data, analyze, results, analysis

Allocating a dedicated TPRM budget isn’t just a necessity — it’s a smart investment. A well-funded TPRM program empowers organizations to proactively identify, assess, monitor, and mitigate third-party risks. Learn more in the infographic.
vendor management budget, TPRM budget, budget, vendor manager budget

As many organizations have turned to cloud vendors to store sensitive information, it's more important than ever to review your cloud vendors. Learn how to in this eBook.
cloud vendor management, vendor risk, cloud vendors, cloud risk, assessing vendors

While there are many benefits of BaaS, these services come with risks on both sides of the partnerships. It’s crucial to identify and assess the associated risks and the measures banks and non-bank entities can take to manage them effectively.
banking as a service risk, banking as a service partnerships, banking as a service vendors, baas vendor partnerships, baas vendor relationship, banking as a service

To manage risks effectively, an organization's risk culture plays a crucial role. A risk culture refers to an organization's mindset and approach toward managing risks. Learn how to develop a third-party risk culture in this eBook.
risk culture, develop a culture, tprm culture, vendor risk culture, vendor management culture, developing risk cultures
Vendor risk management may seem like a large investment, but there's a significant ROI your organization can attain. Understand how a VRM program is a smart investment for your organization.
Whether you're new to the world of TPRM, or an experienced veteran, you've probably heard the term "vendor risk assessment". In the eBook, learn the process of vendor risk assessments and how to overcome challenges.
vendor risk assessment, third-party risk, third-party risk assessment, risk assessments

While vendor relationships can help organizations save money, they also introduce risks and hidden costs. This eBook explores these hidden costs, the consequences of missed risks, and how to manage them.
vendor management, third-party risk management lifecycle, strategic enabler, regulatory compliance, organization strategy
Identifying critical vendors is a necessary process that drives many TPRM activities. In this infographic, learn how to identify which vendors are critical to your organization.
high risk, identifying critical vendor, critical vendor overview, high risk vendor

Inherent and residual third-party risk are interconnected, but they do have differences you should be aware of. Learn the differences between them and how they can affect your organization in this eBook.
vendor management, third-party risk management lifecycle, strategic enabler, regulatory compliance, organization strategy
Writing and updating a third-party risk management policy is known to be time-consuming and without guidance or help, it can be challenging to know where to start. Download this template with accompanying instructions and guide to get started.
free policy template, vendor management policy, third-party risk management policy, policy updates

Learn how to review a vendor SOC report, when to obtain and review a vendor SOC, and key areas to look for.
vendor management, security organization controls, vendor risk

International vendors require unique considerations during the due diligence and contracting process. Learn what to review in this infographic.
due diligence, contract management, overseas, international vendors, international vendor management
Are you prepared for third-party vendor data breach? As cyberattacks occur more frequently, learn next steps to take.
vendor data breach, suffered data breach, vendor data breach next steps, cyber attack next steps
Artificial intelligence (AI) is becoming more prevalent in many organizations - it's no longer a matter of if your vendor is using AI, it's a matter of how. And there's still uncertainties with its risks. Use this questionnaire to get started.
ai vendor risk, ai risk, ai template, ai questionnaire, free ai questionnaire, ai sample vendor questionnaire, artificial intelligence vendor risk
This infographic covers why the board and senior management should set the "tone-from-the-top", responsibility guidelines, and tips to help you gain support.
Organizational buy-in, vendor owners, vendor managers, board of directors, reporting, data
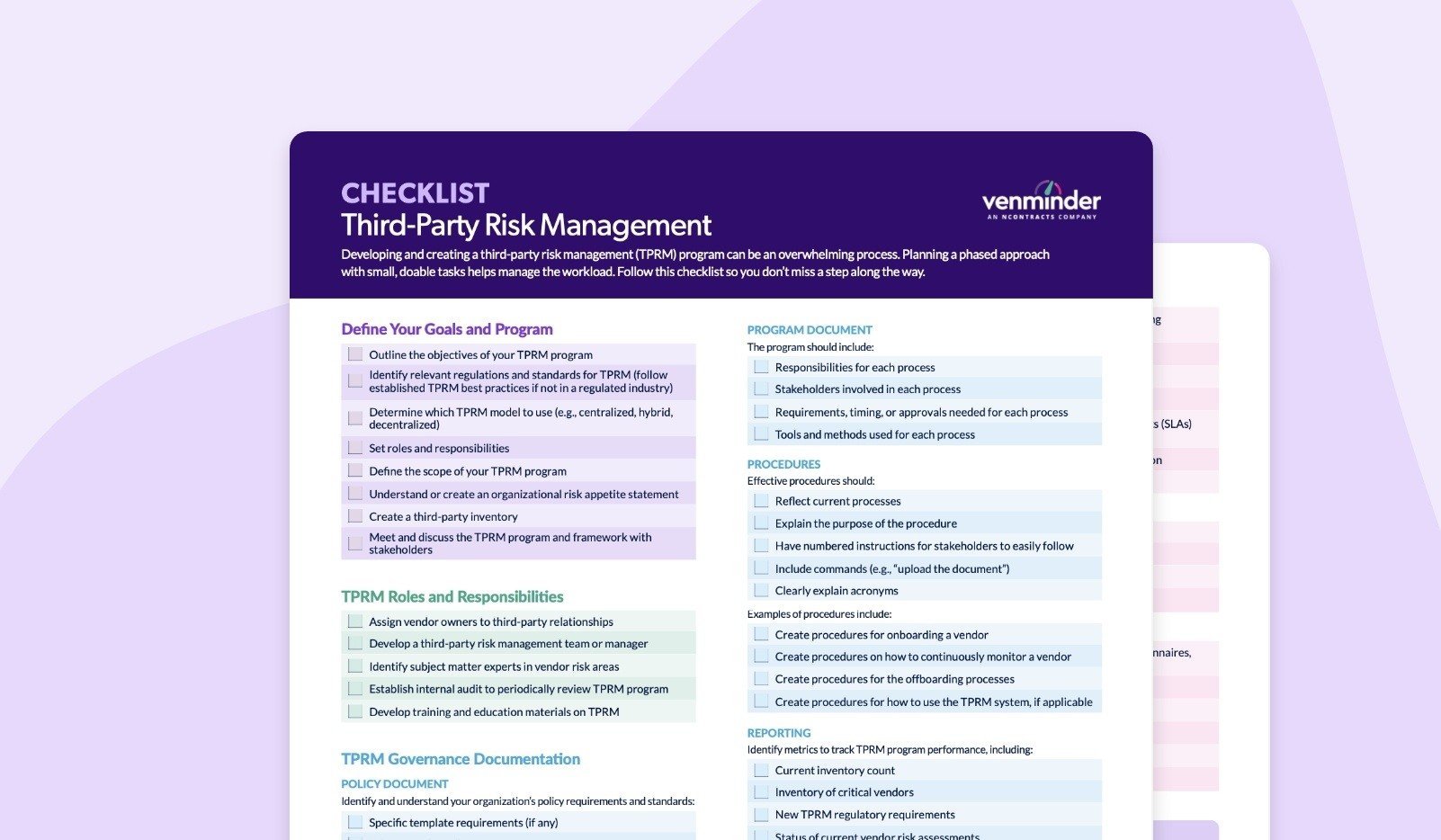
This checklist for creating and implementing a third-party risk management program is designed to help you identify, assess, manage, and mitigate third-party risks. Follow these practical steps to get your program started.

You likely know the importance of managing third-party risks, but what should you do about fourth parties? Fourth parties are essentially your vendor's vendor, or a subcontractor.

Selecting a new vendor can be an exciting yet daunting task. Your organization must identify the right product or service, assess vendor risks, collect due diligence documentation, and remediate any issues. Learn how to select a new vendor in this infographic.
vendor selection, new vendor, vendor onboarding

Third-party risk management (TPRM) governance documentation is the foundation for managing vendor relationships. The policy, program, and procedures define the rules, requirements, and expectations for your organizations TPRM program.
Navigating vendor risk management is filled with challenges and roadblocks. As you manage changing and emerging vendor risks, essential practices like risk assessments, due diligence, contract management, and continuous monitoring will keep you on course.
vendor management
Make sure your vendor risk management program is successful, here 7 are the seven critical items that you need to focus on.
vendor risk management program, vrm program, tprm program, vendor management program, successful program management
Vendor scorecards are a valuable tool to help you track and measure vendor performance. Download this eBook and template to improve your understanding of vendor performance metrics.
vendor vetting, ongoing monitoring, vendor management, performance monitoring, vendor scorecard

For many organizations, managing third parties throughout the entire relationship can be challenging. Utilizing the third-party risk management lifecycle can help. Learn more in this podcast.
tprm lifecycle, lifecycle management, vendor management lifecycle, risk lifecycle, vendor risk lifecycle

Use this as your guide to understand vendor risk management takeaways from the SEC's recent examination priorities report.
vendor risk management, SEC examinations, SEC, regulations, guidance, regulator, guidelines, cybersecurity report, observations resiliency reports
Regulatory guidance and best practices can change, so it's worth reviewing new information as it becomes available. This eBook contains tips to comply with third-party risk management guidelines across different industries and around the globe.
Interagency Guidance, OCC, FDIC, FTC, The fed, FFIEC, CFPB, Securities and Exchange Commission, SEC, NCUA, HHS, tprm regulations, tprm guidance
Learn more about the specific differences between high-risk and critical vendors with this helpful infographic.
high risk vendor, critical vendor, differences between high risk critical vendors

As artificial intelligence becomes more prevalent in vendor products and services, it's crucial to understand how to address the risks in your vendor contracts. This infographic will give you considerations for contract planning, provisions to include, and more.
artificial intelligence risk, ai risk, vendor ai risk, ai considerations, ai vendor contracts

Your organization is solely responsible for implementing CUECs, and failing to do so means your organization isn’t protected from known vendor risks. By identifying, reviewing, and mapping vendor CUECs, your organization can ensure the right controls are implemented.
vendor cuecs, soc report cuecs, complementary user entity controls, mapping cuecs, vendor soc controls,

Third-party risk management is becoming a larger focus area, not only for the OCC, but also for other regulators across the financial industry. Reading and understanding these regulations can help strengthen your compliance program and ensure it's headed in the right direction.
OCC exam priorities, examination priorities, regulatory exam, vendor exam, occ regulations, occ priorities

As you review the cybersecurity information provided, you'll notice that vendors often have a wide assortment of cybersecurity documents available. To help, this infographic breaks down the types of evidence to collect from vendors.
vendor cybersecurity, cybersecurity documents, document collection, vendor cybersecurity documents

Take steps to protect your organization from vendor cybersecurity risk. Listen to this podcast for 6 steps to manage third-party cybersecurity risk.
As cybersecurity risk continues to evolve it's getting more challenging to identify and manage. Learn next steps to address a vendor's poor cybersecurity practices in this infographic.
poor cybersecurity practices, cybersecurity red flags, vendor cybersecurity risk, cybersecurity practices
Ensure you're getting the most out of your third-party risk management resources. Download this eBook to get a better understanding of which of your third parties or vendors are determined in scope or out of scope.
vendor management, exclusion, inclusion, in scope third parties, out of scope third parties
Lean third-party risk management teams and large vendor inventories only add to the complexity and work effort, especially if the program's TPRM process involves manual processes, etc. In this eBook learn how TPRM platforms support your program, regardless of maturity.
outsourcing tprm, outsourced vendor management, when to outsource, outsourcing vendor management processes, outsourcing tprm task, mature program, new program
This infographic breaks down the elements you should look for in vendor business continuity and disaster recovery plans.
bdcr, bcdr plans, bcp, drp, business continuity management, business impact analysis

There are three vendor risk management frameworks to consider: centralized, decentralized and a hybrid approach. We'll teach you the differences and guide you toward the best framework for you.
Ongoing monitoring isn't a one-time process, but rather a series of activities based on the third party's risk. Learn tips and best practices for ongoing monitoring in this eBook.
third-party ongoing monitoring, ongoing monitoring, monitoring third-party risk, risk monitoring, continuous monitoring

Mapping out your annual budget for third-party risk management can be challenging. Developing a budget roadmap is one way to tackle these challenges head on. Download the eBook to learn more.
third-party risk budget, budgeting, budget roadmaps, vendor management budget, tprm budget, budget allocation
Lack of preparation in advance of the contract end date leaves little time for negotiation or modification. Mid-term contract reviews are effective to ensure your vendors continue to deliver products and services as expected.
vendor contract management, contract assessment, mid-term agreement, vendor agreement
Incorporate sound contract compliance techniques to lessen exposure to vendor risk and improve contract management practices. Use these techniques to help you with the process.
contract negotiation, contracts, vendor contract compliance, vendor contracting, contract management

If your organization is in a regulated industry, you should anticipate regular examinations. It's good to review your regulators website to become familiar with their exam process, classification of issues, etc. In this podcast, learn common exam findings and next steps.
vendor management exams, vendor management exam findings, tprm exam findings, tprm exam, third-party risk management exams

As organizations continue to rely on outsourced products and services, the rapid deployment and wide variety of AI use brings about many news risks that require careful consideration. This eBook explores the risks associated with third-party AI.
third-party ai, ai risks, third-party ai risk, vendor ai risk, artificial intelligence risks
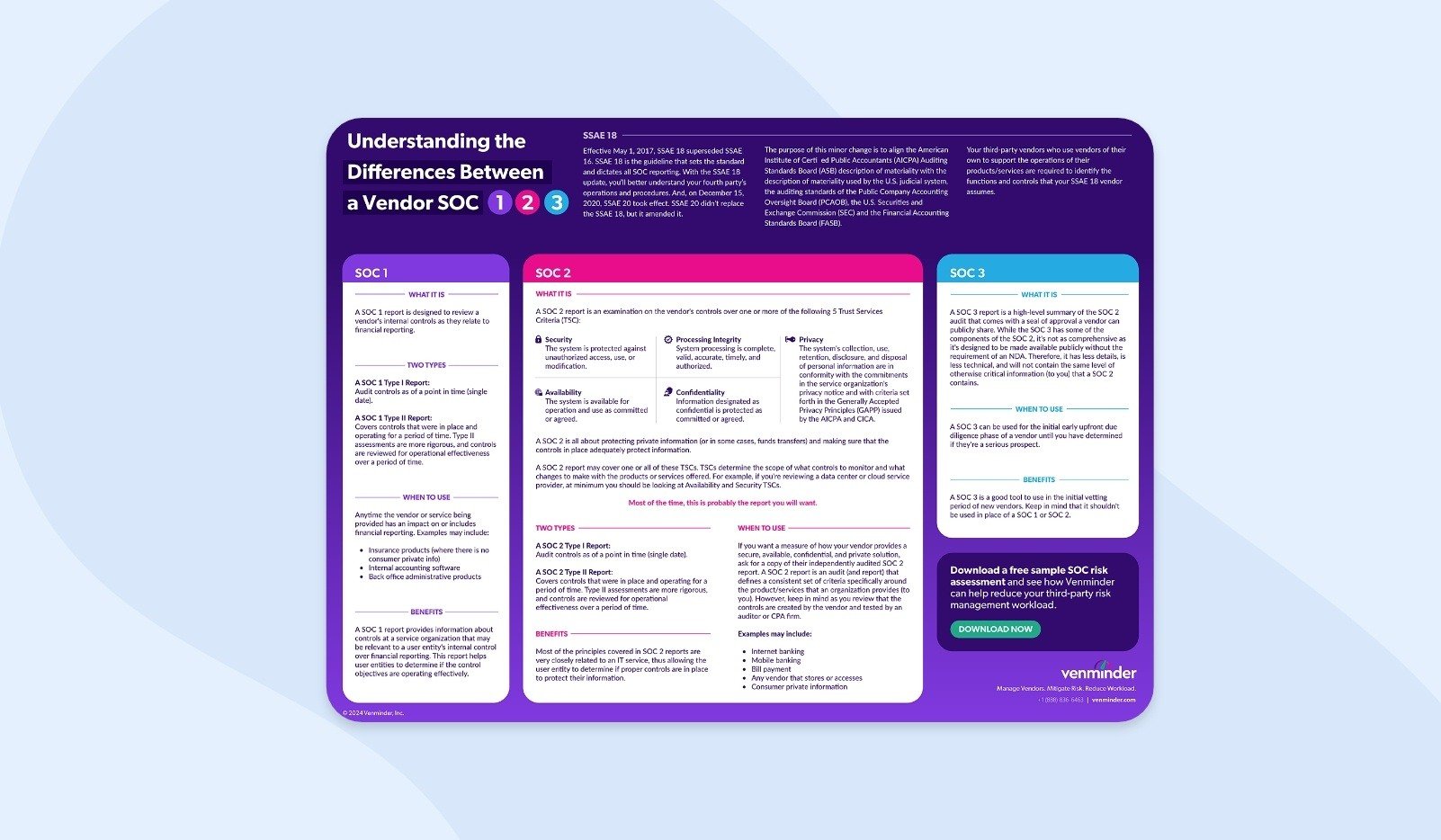
Download the infographic to learn the definitions of each type of SOC report and how they can benefit your organization.
information security, soc report, vendor soc, vendor soc 1, vendor soc 2, vendor soc 3
Vendor performance must be closely monitored and tracked to ensure it remains at the expected level outlined in the service level agreement. Learn how to use key performance indicators to maintain SLAs in this eBook.
strong vendor relationships, kpis, key performance indicator usage, strong SLAs, maintaining slas

Vendor data breaches can range in severity, from minor incidents to significant events that create operational failures and require public disclosure. Protect your organization by learning about the different categories and types of vendor data breaches.
vendor breach, data breach, types of data breaches, tips to prevent breaches, breach, third-party breach

A vendor's insurance can reduce the financial risk posed to your organization. This eBook explains how your organization can better align its use of vendor insurance coverage as a risk mitigation technique.
vendor insurance, insurance coverage, financial liability, reduce financial liability, third-party insurance, certificate of insurance

Anyone who's involved in vendor risk management knows the intricacies of the various tasks. In this podcast, learn tips and commons ways you can utilize VRM software to streamline your processes
vrm software, tprm software, streamlines processes, streamline vendor management tasks, streamline tprm tasks

There are many consequences that can arise from a vendor’s poor financial performance. In this infographic learn strategies and tips to help your organization use relevant contract language and SLAs to address a vendor’s poor financial health.
poor vendor performance, vendor financial performance, SLA, vendor contracts, service level agreements, track vendor financial health

As relationships between fintech organizations and credit unions have revolutionized the industry, third-party risk management has become more crucial for both parties to have. Learn how third-party risk management has evolved for credit unions and fintech in this panel interview.
fintech, credit union, panel interview, industry expert interview, financial technology
The North American Electric Reliability Coporation's (NERC) standard, CIP-013-1 Cyber Security - Supply Chain Risk Management requires effective vendor risk management in the energy industry. Learn how to comply in this eBook.
nerc regulation, north american reliability corporation vendor management, vendor risk management regulation, energy organization, energy company, energy risk management

Vendor risk management is a complex practices that requires a thorough understanding of your organization's objectives, regulatory requirements, and vendors' business practices. Follow the tips and best practices in this mini handbook to help you maintain an effective vendor risk management program.
vendor management, third party risk management, vendor management handbook, risk management handbook

With the number of vendors in an organization, it may not always be obvious where a vendor sits on the high-low value spectrum. This eBook will help you determine who your low and high-value vendors are, and how to get the best value from your vendors.
vendor quality, vendor risk, operational risk, reputation damage, due diligence, performance management, vendor owner, vendor manager
While you can't eliminate all the risks posed by your vendors, you can reduce them by following the steps of the third-party risk management lifecycle. Watch this video to learn how to effectively manage third-party risk.
mitigate third-party risk, managing vendor risk, mitigate vendor risk, how to manage vendor risk, effective tprm, effective vendor management, third-party risks, vendor risks
Managing vendor risks is crucial to the success of any business. It requires identifying all potential risk associated with products and services provided by a vendor. Learn the steps to complete the vendor risk assessment process in this infographic.
vendor risk, vendor profiling, questionnaires, risk assessment process, assessing vendors
Vendor due diligence is one of the most vital activities within third-party risk management. But, it's not always clear when and how often vendor due diligence should be done. By following these recommended guidelines for the frequency of due diligence, you can ensure your time and efforts are well spent.
vendor due diligence process, perform due diligence, perform vendor due diligence, when to perform due diligence, how often perform due diligence

The success of a TPRM program depends on a carefully integrated combination of rules, tools processes, and people. In this eBook, learn the existing roadmap, known as the third-party/vendor risk management lifecycle and more.
vendor risk management, risk management, third-party risk management lifecycle, vendor risk, mitigate risk
This complimentary toolkit includes reporting (annual and monthly) templates and provides you with guidance on how to format vendor board reports.
third-party risk reports, board reporting, report vendor risk management activity, report third-party risk management activity, reporting
One of the first activities in the third-party risk management lifecycle is completing an inherent risk assessment. This process identifies the different types and levels of inherent risk, which occur naturally within the vendor’s product or service. Learn the steps to complete an inherent risk assessment in this infographic.
vendor inherent risk, risk assessment process, vendor risk assessments, how to complete risk assessments, due diligence

In this podcast we’ll discuss 4 important vendor risk management frequently asked questions for beginners to help get you started. The questions like: what vendor risk management is, why it’s important, who is involved and how vendor risk is completed.
vendor risk management beginner, beginner tprm, tprm frequently asked questions, beginner vrm, vendor management question, third-party risk management questions

It's critical to take into account recent best practices in order to be as prepared as possible for vendor management. This eBook has 31 best practices everyone should know.
vendor management best practices, best practices, third-party risk best practices, vendor risk best practices
The first stage in a third-party risk management program is onboarding any new vendor. There's a lot to consider in this stage, including risk assessments, due diligence, and more. This toolkit will help ensure your vendor relationships starts of on the right foot.
how to onboard vendor, vendor onboarding, onboarding vendors, steps onboarding vendor, stage of lifecycle, third-party risk management lifecycle onboarding

As part of vendor risk management, you need to know your third party's financial condition. Download a free analysis on your core vendor now.
financial health sample, sample, free assessment

Maintaining regulatory compliance with third-party vendors can be challenging, especially when it comes to cybersecurity guidance and state privacy laws. Learn key cybersecurity regulations and tips to strengthen compliance in this infographic.
vendor cybersecurity, cybersecurity preparation, preparing for cybersecurity regulations, state privacy laws
Cybersecurity threats will always exist, but maintaining regulatory compliance can help your organization prevent and respond to events more effectively. Learn who must comply with 23 NYCRR 500, highlights of the regulation, and more.
regulatory compliance, guidance

Building a fourth-party vendor inventory can be challenging, but it's crucial to protect your organization from an extensive risk landscape. This podcast explains how to build a fourth-party vendor inventory and tips to keep in mind.
vendor inventory, inventor building, fourth-party risk, fourth parties, build inventory, tips building vendor inventory
Reviewing a vendor’s financials is an essential step of every successful third-party risk management program. Comparing this data to financial benchmarks is an effective strategy that can bring greater clarity to your vendor’s financial health. Learn more in the eBook.
vendor financial benchmarks, financial reviews, benchmarking, reviewing financial data, financial data, third-party financial review, third-party financial benchmarks

Use this as your guide to understand vendor risk management takeaways from the SEC's recent examination priorities report.
vendor risk management, SEC examinations, SEC, regulations, guidance, regulator, guidelines, cybersecurity report, observations resiliency reports

Conducting risk-based due diligence on your vendors can help you streamline your vendor reviews. In this podcast, learn 3 ways risk-based due diligence can improve your efficiency.
risk-based due diligence, vendor risk due diligence, risk-based, due diligence, vendor due diligence, conduct due diligence, risk assessment, risk profiling

In this thought leadership interview, Rachael Ormiston, Head of Privacy at Osano discusses how to implement vendor privacy scores in your third-party risk management practices.
privacy score, vendor privacy, privacy score benefits, privacy risk
Reviewing a vendor's business continuity and disaster recovery plans is an essential step in your due diligence process. A weak finding as you assess plans should be concerning, as this can expose your organization to significant risks. Learn more in the infographic.
business continuity testing, bcp, business continuity planning, weak bc/dr plans, weak business continuity, vendor business continuity, vendor disaster recovery

Third-party risk management is a highly rewarding practice for an organization and its stakeholders, but it can be difficult to understand the value this practice can bring. This business case for third-party risk management explores why your organization should invest in this essential area.
business case tprm, tprm business case, vendor management business case, outsourcing risk, outsourcing third-party risk management activities, buy-in, invest third-party risk management
Effective vendor contract management has many benefits that all organizations can experience, including potential cost savings and safer third-party vendor relationships. Learn effective contract management practices in the infographic.
vendor contract management, vendor contract risk, contract management risk, vendor contracts, contract risk, effective contract management, contract management practices

Without the right documents, your vendor risk assessment can't be completed correctly, if at all. In this infographic, learn best practices and tips to improve document collection efficiency.
document collection, vendor due diligence, due diligence, vendor documents, documents

New to third-party risk management or looking to stay up-to-date on a wide range of industry topics? This interactive guide is full of resources for beginners.
vendor management, risk management, third-party risk management resources

Level up your third-party risk management knowledge with this interactive guide. Continually improve your knowledge, program and more!
vendor management, risk management, third-party risk management resources

Understanding the key roles involved in third-party risk management is important to you and your organization. Learn their responsibilities and how they fit into your third-party risk management program.
vendor management, involvement, staffing
Having an effective planning process will justify the need, cost, and benefits of a vendor relationship and start your onboarding process on the right foot.
onboarding a vendor, planning onboarding, planning steps,
For the vendor performance management process to be effective, organizations must think carefully and plan ahead. An effective process helps reduce costs, enhance customer satisfaction, mitigate risks, and more.
vendor performance, performance management, performance process, vendor performance process, managing vendor performance, performance questions

The economy has faced many challenges the past few years. These events present many challenges for organizations, and some are looking to cut costs. But, reducing TPRM may be a mistake as it can help protect your organization.
reduce costs, cut third-party risk management, economic climate, cutting costs, reduce budget
The program document answers the "how" of each third-party risk management activity. In this infographic, learn how to write an effective third-party risk management program document.
third-party program document, write policy and program, program writing, program document, write third-party risk management program document

Third-party compliance risk can be one of the more challenging areas to manage, but it's necessary to protect your organization from significant consequences. Use the 6 techniques covered in this infographic.
compliance management, vendor compliance, third-party compliance, manage compliance risk, manage vendor compliance

In this thought leadership interview, Andrew Moyad, CEO at Shared Assessments, discusses the importance of cyber insurance in third-party risk management. Learn what it covers and how it can help protect your organization from third-party cyber risk.
vendor cybersecurity, cyber insurance, cybersecurity insurance, infosec insurance, cybersecurity risk
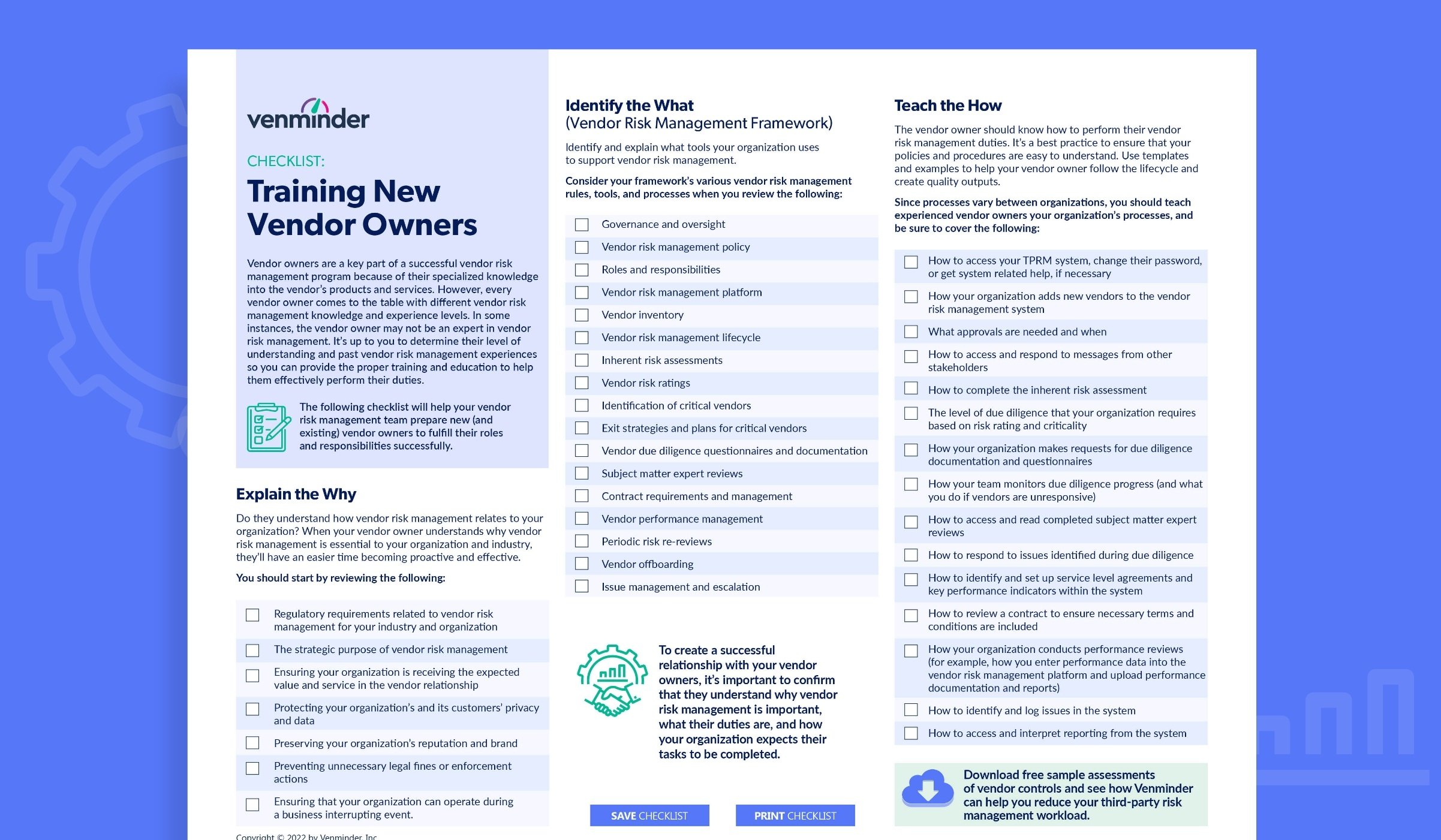
Have new or existing vendor owners that need to be trained? This checklist will help your vendor risk management team prepare vendor owners to fulfill their roles and responsibilities.
checklist, vendor owners, vendor management, vendor manager
When you learn the key steps, building a vendor risk management program doesn't have to be an overwhelming task. Organizations of all sizes can build a program that will satisfy regulators and manage vendor risk.
vendor management, effective vendor risk management program, program building, building a program, vendor risk management program

Learn 4 key recommendations to implement in your third-party risk management programs to mitigate third-party risk this upcoming year. Listen now.
third-party risk management best practices, tprm best practices 2024, third-party risk recommendations, tprm recommendations, best practices for 2024, cybersecurity recommendations, data breach recommendations, due diligence recommendations
There isn’t a one-size-fits-all solution to third-party risk management policies. This eBook will help you understand the dos and don'ts for creating a policy and best practices.
vendor risk management policy, risk management policy, creating policy, updating policy, tprm policy, third-party risk policy
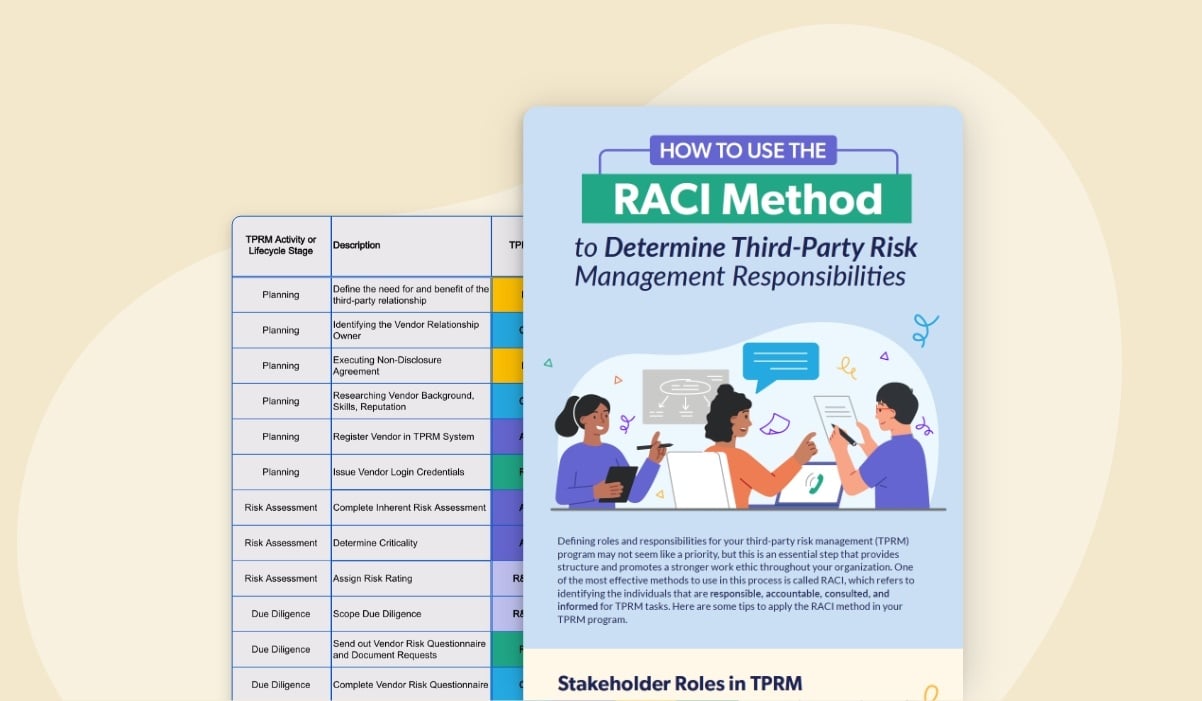
Defining the roles and responsibilities within your TPRM program is crucial for success. Learn how to implement the RACI method with this infographic and customizable template.
raci method, roles and responsibilities, tprm roles, tprm responsibilities, organizational structure

In this thought leadership interview, Tom Rogers, Vendor Centric, defines the characteristics that make up a fourth-party vendor and uncovers the steps to manage them. Listen to this interview to learn about fourth-party due diligence, regulations, and best practices.
fourth parties, fourth-party vendor, thought leader interview, managing vendors

Learn best practices that should be included in your third-party risk management program to ensure you keep your organization protected from data breaches and other cybersecurity incidents.
third party risk trends, third-party risk management, best practices, tprm best practices, tprm trends, svb, republic bank, signature bank
Without collaboration, organizations can face many challenges. In the eBook, explore some ways InfoSec and TPRM can proactively partner to benefit both teams.
information security, collaboration, better risk management, collaboration benefits
Learn the necessary actions to comply with Canada's Office of the Superintendent of Financial Institutions (OSFI) final Third-Party Risk Management Guideline B-10.
regulations, governance, compliance, FRFI, federally regulated financial institutions

If your organization doesn't have the right vendor risk management practices, your organization's and customers' data is at risk. To protect data, you must understand how your vendors plan to use it and safeguard it.
data privacy, cybersecurity, information security, lines of defense, third-party risk management lifecycle, documenting, reporting

Vendor data breaches will always be unexpected, but it’s possible to anticipate your response, which can minimize the damage to your organization and customers.
cybersecurity, information security, breach notification, data privacy, reputational damage, operational disruptions, cybersecurity posture

It's increasingly common for healthcare organizations to experience a data breach stemming from a business associate. Learn the 6 key steps to prepare your organization for a breach.
data privacy, reputational damage, operational disruptions, breach notification, information security, cybersecurity
An effective third-party risk management program provides many strategic advantages to an organization. One obvious benefit is meeting regulatory requirements, but there's a much broader range of benefits.
SLA, service level agreement, operational advantages, outsourcing

Learn best practices that should be included in your third-party risk management program to ensure you keep your organization protected from data breaches and other cybersecurity incidents.
breach notifications, cyber right to audit, data protection, information security, data privacy, infosec

While technology sophistication is growing, so are the capabilities of hackers. Use this infographic to learn how to build a solid defense against cybersecurity risks.
data breach, information security

Mike Morris talks about the proposed SEC Outsourcing Rule and its impact in vendor risk management. Listen to learn answers to common questions, tips, and suggestions, as well as a general overview of the proposed rule.
regulations, financial services, fintech, guidance, registered investment advisors

This eBook explores how you can articulate the many requirements and benefits for your stakeholders to enhance their understanding and improve their third-party risk management program buy-in.
board reporting, stakeholder buy in, vendor owners, vendor managers, implementing third-party risk management platform, outsourcing,
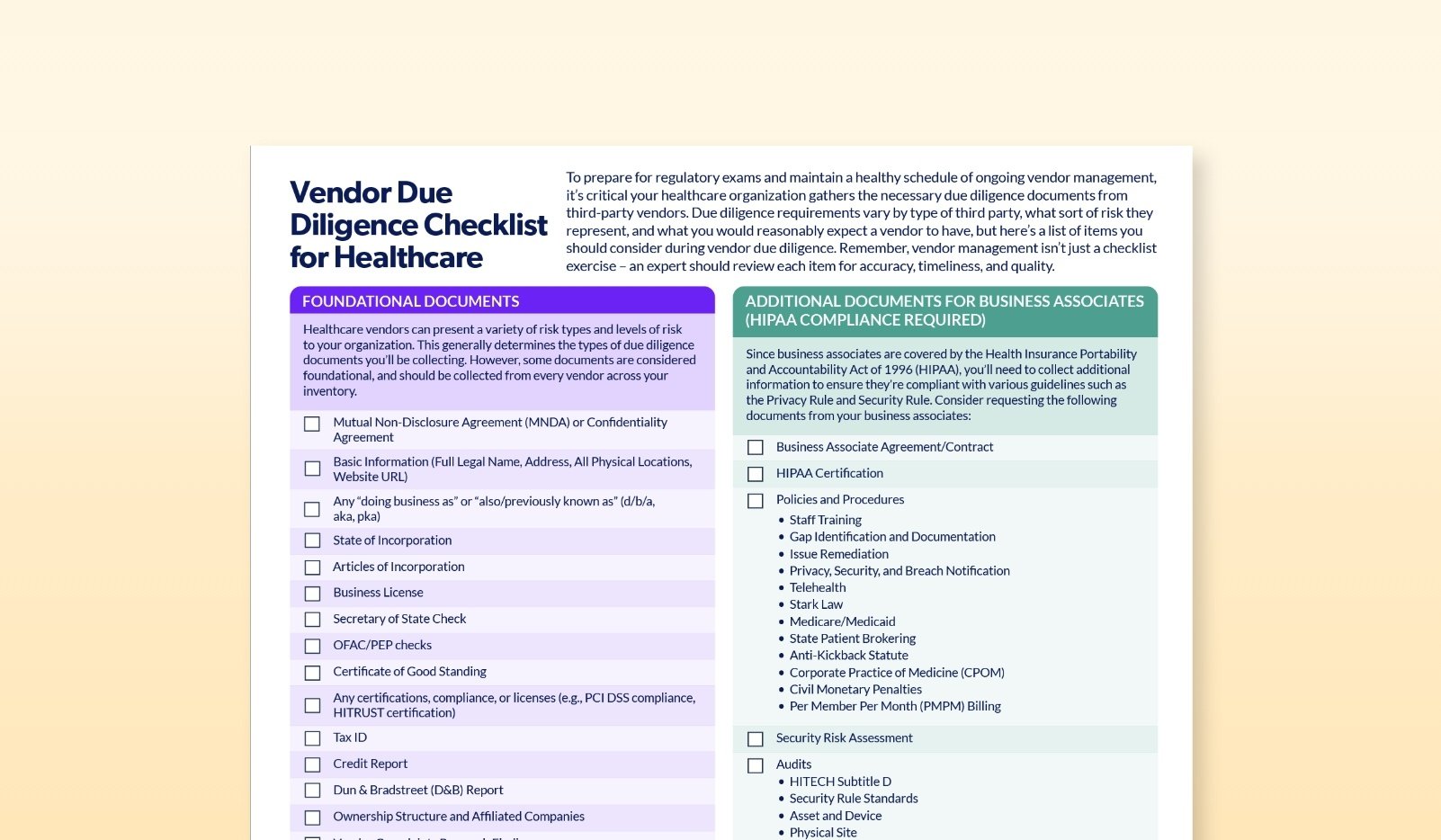
There are many due diligence considerations unique to healthcare organizations. Use this handy checklist when thinking through the vendor due diligence you should be assessing, and the foundational documents to request from every vendor.
document collection, ongoing monitoring, continuous monitoring, hipaa compliance, ongoing vendor management, business associates
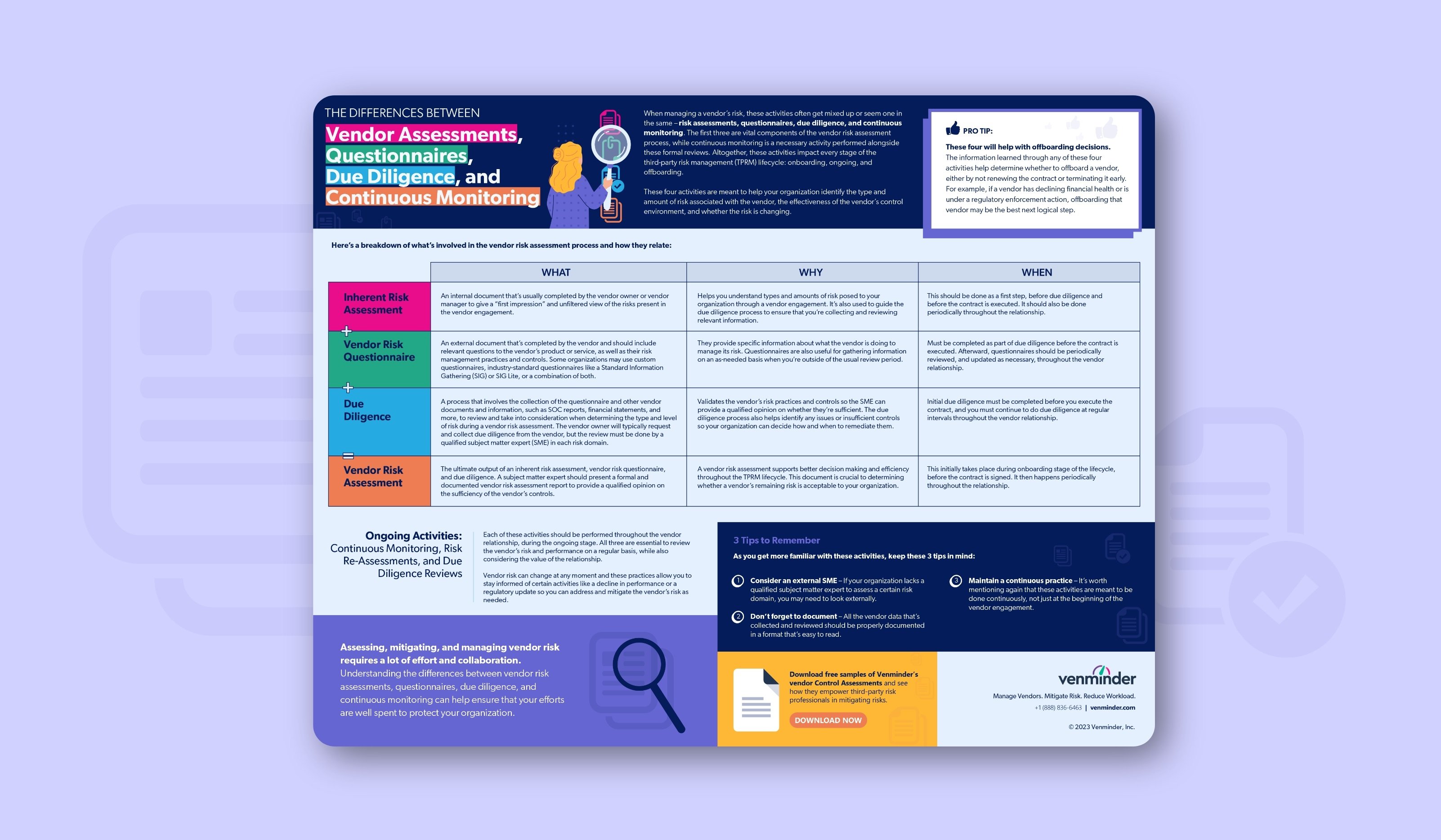
While all are important, there are differences to be aware of between questionnaires, risk assessments, due diligence, and continuous monitoring.
ongoing monitoring, risk re-assessments, vendor offboarding, third-party risk management lifecycle
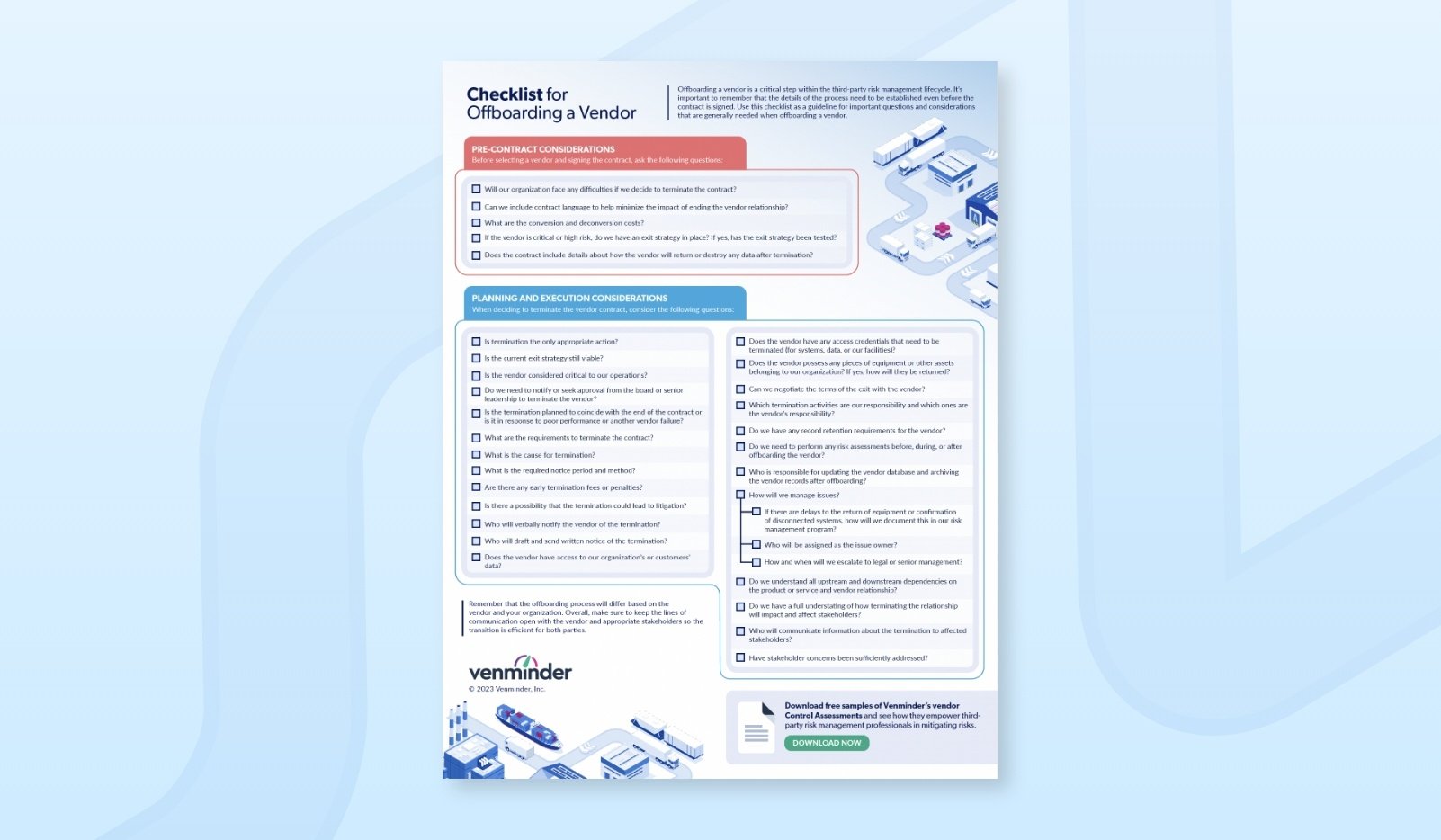
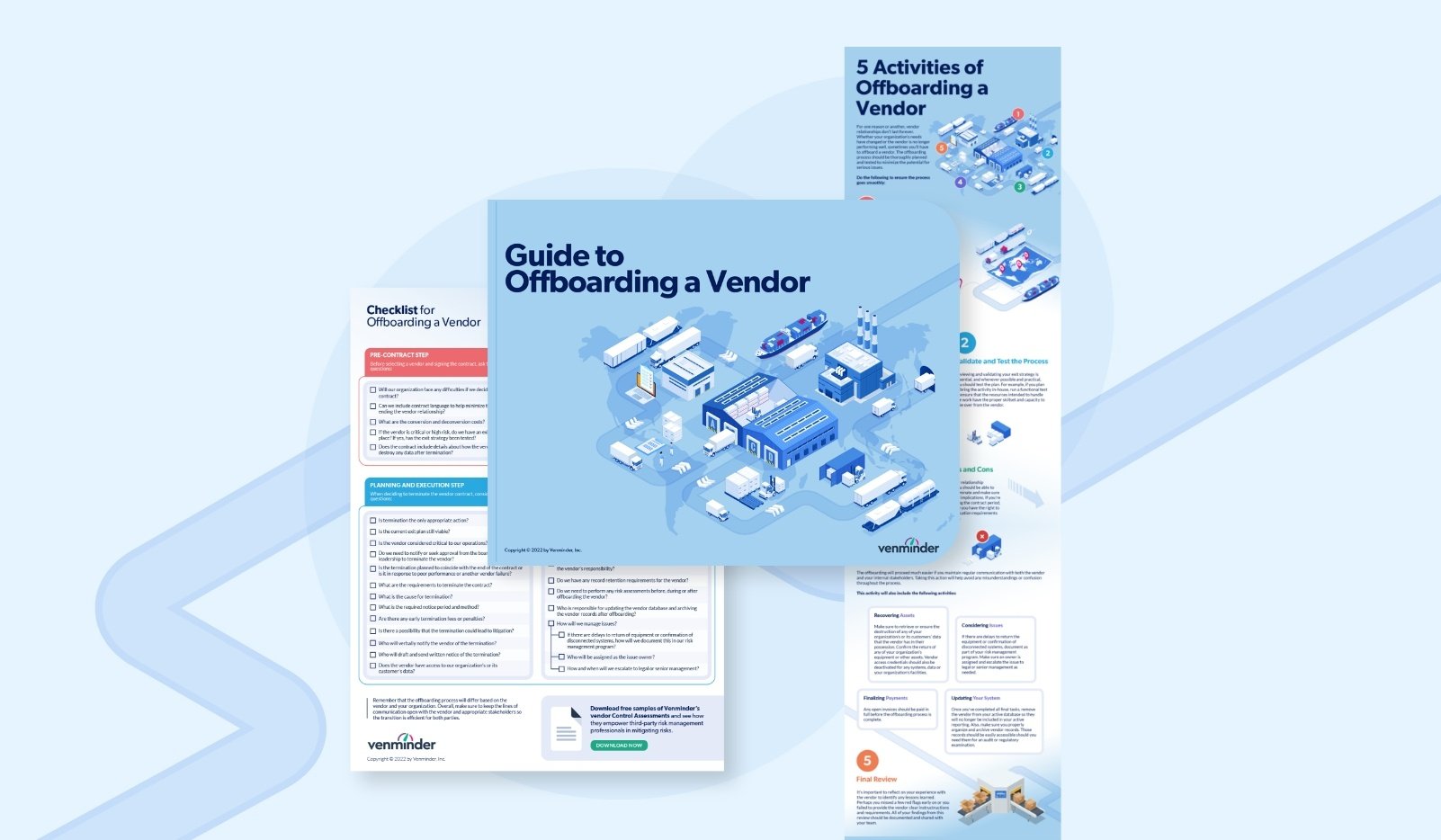
Offboarding a vendor is a critical step within the third-party risk management lifecycle. The process will differ based on the vendor and your organization, and details of the offboarding process need to be established before the contract is signed. Use this checklist for important considerations when offboarding a vendor.
offboarding a vendor, vendor offboarding, offboarding, exit strategy, offboarding checklist
The Board, FDIC, and OCC released the official interagency guidance on managing third-party relationships. This eBook gives you 7 takeaways you should be aware of.
regulations, banking, vendor scope, critical vendors, due diligence, ongoing monitoring, documentation, reporting

Regulatory examiners have distinct expectations when it comes to the boards involvement in third-party risk management. Listen to learn the board's place in regulatory exams, and how you can lend a helping hand.
TPRM, regulations, regulatory exams, contract management, audit, due diligence

Learn the key takeaways from important third-party risk regulatory guidance released by the OCC, FDIC and FFIEC from our compliance expert.
regulatory guidance
Some healthcare organizations will accept an independent audit report in lieu of a vendor completing an assessment questionnaire. In this infographic learn what to look for in a vendor's SOC 2 Type II audit report and key elements to review.
risk posture, risk assessment, audit report, cybersecurity, PHI, protected health information, healthcare due diligence

Larger vendors can be more difficult to manage. Learn essential tips and best practices to mitigate vendor risk with your large vendors in this podcast.
large vendor inventory, large vendors, vendor risk, mitigate vendor risk, mitigate large vendor risk, manage large vendors
What do you do if a vendor's SOC report is filled with issues? Use this infographic as a guide to determine how to proceed with the vendor, whether that's addressing the issues or passing on the vendor relationship.
cybersecurity, due diligence, regulatory audit, vendor offboarding, controls
This eBook explains what vendor risk management is and how you can implement it. Done right, a good vendor risk management program creates a real strategic advantage for your utility company.
risk mitigation, continuous monitoring, ongoing monitoring, third-party risk management

Use this infographic as a guideline for important data to collect and continuously update. Ensure that the appropriate stakeholders are well-informed to drive action in your third-party risk management program.
document collection, risk assessment, ongoing monitoring, issue management, Inventory

ESG is a rapidly growing business principle that aims to better measure the success and sustainability of an organization. This eBook provides steps to implement ESG into your TPRM program successfully
CSR, corporate social responsibility, environmental, social, governance

By understanding your vendor's cybersecurity posture and doing the appropriate steps to prevent risk, you can reduce the chances of your healthcare third parties compromising you.
inherent risk, due diligence, information security, infosec, controls, HITRUST, data breach

Not all vendors have the same level of risk. Risk-based vendor due diligence can save your organization time and resources in your vendor risk management program. But, do you know the steps to take and when? This informative video explains the 7 steps.
third-party risk management lifecycle, inherent risk, risk level, risk questionnaire, critical vendor, low-risk vendor
Prioritizing TPRM is essential, even if your resources are limited. There are many advantages in utilizing third-party risk management tools. Listen to this podcast to learn more.
third-party risk management resources, leverage resources, tprm resources, limited resources, software
An effective TPRM program requires strategy to identify, address, and resolve any issues in a timely manner. Vendor relationships will never be perfect, issue management is a necessary component that will help prevent larger problems down the line.
issue management, managing vendor issues, vendor issues, risk management issues

Developed by industry experts, you can reference this third-party management glossary for key words in the vendor management process.
third-party risk terms, tprm terms, tprm terminology, understanding third-party risk management terms
Higher education institutions have become increasingly dependent on the utilization of third-party vendors in today's climate. In this eBook, learn the importance between TPRM and higher education.
higher education, school districts, higher education TPRM, higher learning vendor risk
Risk-based vendor due diligence can save your organization valuable time and resources. In this infographic learn what vendor risk-based due diligence is and why it matters
Vendor due diligence, risk-based due diligence, level of risk, due diligence frequency
It's not surprising that most sponsoring small pharma and biotech startups choose to perform their clinical trials with the assistance of CROs. But, not all CROs are created equal, so selecting the right CRO is crucial.
biotech, due diligence, vendor due diligence, contract research organization selection, CROs

Collaboration with vendor owners involves a lot of day-to-day activities, spanning across the three stages of the third-party risk management lifecycle. This podcast outlines tips to improve collaboration between your third-party risk management team and your vendor owners.
vendor owner, training vendor owner, vendor management

Not all of your third-party relationships will end naturally at the end of a contract period. Sometimes, early contract termination is needed, so your organization must be prepared. This eBook outlines the necessary steps.
vendor offboarding, proactive termination, reactive termination, periodic reviews, third-party contracts

Not sure where to begin in implementing a third-party risk management program? Download this eBook to learn the foundational components of a third-party risk management framework.
vendor management, third-party risk management lifecycle, scoping, onboarding, operating model, contract management
Use this as your guide to understand vendor risk management takeaways from the SEC's recent examination priorities report.
vendor risk management, SEC examinations, SEC, regulations, guidance, regulator, guidelines

For a third-party risk assessment to be effective, you must know what kind of data they can access within your network and what kind of data they will access, process, transmit, or store on their networks. Learn more in the infographic.
vendor risk assessment, healthcare risk assessment, healthcare vendor management, healthcare vendor

The HITRUST certification ensures that a healthcare organization has met the requirements outlines in the HITRUST Cybersecurity Framework (CSF). This eBook outlines how to review your vendor's HITRUST certification.
HITRUST certification, HITRUST, review of HITRUST, cybersecurity framework

No matter the vendor, there may be issues that arise at any point in the vendor relationship. In this podcast, learn examples of third-party risk management issues you may encounter and what to do next.
issue management, vendor issues, vendor issue management, third-party risk issues
Successful TPRM programs should involve key metrics that evaluate a vendor's health and stability. To help you better understand how to develop key metrics for your TPRM program, we've created this informative infographic.
key metrics, KPIs, third-party risk metrics, develop metrics

Natural disasters and cyberattacks are just two examples of business disrupting events that occur in the supply chain. This podcast outlines four examples of how TPRM can help you mitigate supply chain risk.
supply chain risk, mitigate supply chain risk, third-party risk management best practices

Whether you’re creating your program for the first time, or revising it, here are 8 best practices.
There's a lot to know to have a successful vendor risk management program. This infographic breaks down the what, why, who, and how to help.
risk management, involved in vendor management, third-party risk management, vendor risk management basics, beginner vendor management
What is vendor management and where to start, what you should know to mitigate risk, vendor lifecycle stages, who's responsible for what in a typical lifecycle and useful links and resources.
third-party risk management, to-do list, vendor management
In today's business climate, vendor financial health monitoring is extremely important. There are several factors to consider when reviewing vendor financial health, including inflation, political instability, and more.
vendor financial health, financials, vendor financials, financial importance
Vendor risks are always present. Although you can't eliminate the vendor's inherent risk you can lessen the likelihood by identifying and implementing controls. In this infographic, learn the process of inherent to residual vendor risk.
inherent vendor risk, residual vendor risk, inherent to residual risk process
Healthcare organizations must know how their vendors access, transmit, and store PHI and other sensitive data to remain compliant to protect their organization's and patient's data. Learn more in the eBook
hospital data, healthcare vendor management, healthcare organization, hospital risk management
Tasked with building a third-party risk management program from scratch? Developing and implementing a TPRM program requires considerable planning and coordination. This step-by-step guide will help you get started.
vendor management program, risk management program, TPRM program, third-party risk program

After conducting our State of Third-Party Risk Management Survey in November of 2022, we've analyzed the results and found six key highlights you should be aware. Listen to this podcast to find out what they are.
state of tprm, third-party risk management highlights, best practices, cybersecurity

It may be time to revisit your third-party risk management program. This eBook walks you through 12 ways you can start to improve your third-party risk management program.
program improvement, improve third-party risk management program, vendor management program improvement, improve vendor management
Most clinical studies are being conducted with the assistance of third-party vendors. Learn how clinical trial oversight remains a critical activity for sponsor organizations in this eBook.
healthcare vendor management, contract research organizations, CRO, clinical trial oversight

Even in today's remote working environment, you need to perform on-site vendor visits. In this podcast, we'll highlight 6 reasons on-site vendor visits are a valuable part of your due diligence practice.
vendor visits, on-site visit, vendor management, due diligence

A standardized and repeatable vendor risk assessment process is essential to protect your organization and customers from avoidable risks. In this eBook, we'll walk you through what you need to know for effective and efficient assessments.
risk assessment, vendor risk, risk assessment guide, vendor risk management
Identifying requirement and best practices for your industry, and following the TPRM lifecycle are great building blocks when implementing TPRM programs. Learn more in this guide.
vendor risk management, TPRM, vendor risk, essential guide, lifecycle, roles and responsibilities, program essentials
TPRM is a complex process that involves many rules, requirements, and processes all of which must be documented. This eBook will explain each of the governance documents and more.
vendor risk management, governance documents, vendor management policy, tprm documents, third-party risk governance documents

2022 was challenging for some organizations this year. In this podcast, learn six third-party risk management best practices to bring into 2023.
best practices, new year, vendor management, third-party risk

Contract research organizations (CROs) demonstrating strong vendor risk management programs can help sponsors feel their exposure to risk is well managed. In this eBook, learn the importance of sound vendor risk management for CROs.
CRO, contract research organization, outsourcing, clinical trial, risk exposure, due diligence, ongoing monitoring, third-party risk management program, vendor risk management, vendor risk

What does it mean for a healthcare organization to perform a risk assessment on a vendor? Is it a questionnaire, review, or process? Learn what a vendor risk assessment entails in this eBook.
healthcare, healthcare vendor management, risk assessment

In order to properly manage your vendors' associated risk, you need to thoroughly understand your organization’s vendor risk appetite statement. Use this infographic to help.
third-party risk management, vendor risk appetite, risk appetite statement, vendor risk

Third-party risk management involves many activities that can take up a lot of your team's time and resources. Listen to this podcast to learn 5 advantages of outsourcing TPRM tasks.
outsourcing vendor management, outsourcing tprm, outsourced vendors, third-party risk management tasks

The two most common reports, the SOC 1 and SOC 2, each assess a different scope of the vendor's controls and performance. In this infographic, you'll learn the difference between the two and which report you'll want to request.
vendor soc, soc reports, request soc report, SOC 1 report, SOC 2 report

A cybersecurity incident can have detrimental effects on your organization's financial health, reputation, and more. In this eBook, we'll cover why cybersecurity and business continuity are linked.
cyber risk, cybersecurity risk, vendor cyber risk, BCP, cybersecurity measures

Protecting your customers' sensitive information is important. In this podcast, learn ways to safeguard your organization from third-party cyber risk.
cybersecurity, vendor cybersecurity, cyber risk, cybersecurity risk

Establishing clear expectations with your vendor from the earliest stages of entering a relationship is important. There are two clauses that are essential, learn more about them in this infographic.
right to audit, cybersecurity, information security, data protection, data breaches, vendor management

You've completed your vendor risk assessment, performed due diligence, and have identified the inherent risk the vendor brings. This eBook highlights examples of ways your organization can improve the security of a vendor's system in your network.
mitigate risk, vendor risk, healthcare vendor risk, healthcare vendor management, third-party vendor risk, hipaa
Due diligence is a fundamental component of any third-party risk program. We will break down how to do vendor due diligence reviews on 6 of the most common reports we do.
ongoing monitoring, oversight, vendor management, due diligence

Venmonitor™ is a new software tool that brings the industry’s best risk intelligence data into one central location, allowing you to easily screen vendor or supplier performance across multiple risk domains.
venmonitor sample, risk intelligence data, risk domains, risk management, software

Critical vendor contract management is important. Learn 4 best practices in this podcast to ensure your monitoring your critical vendor contracts.
contract management, vendor contracts, critical vendor, podcast, critical vendor contracts
Many often ask "how many people should you dedicate to third-party risk management?" Even regulatory guidance offers little assistance in this area. Learn considerations, industry data, and more in the eBook.
vendor management, staffing, TPRM staffing
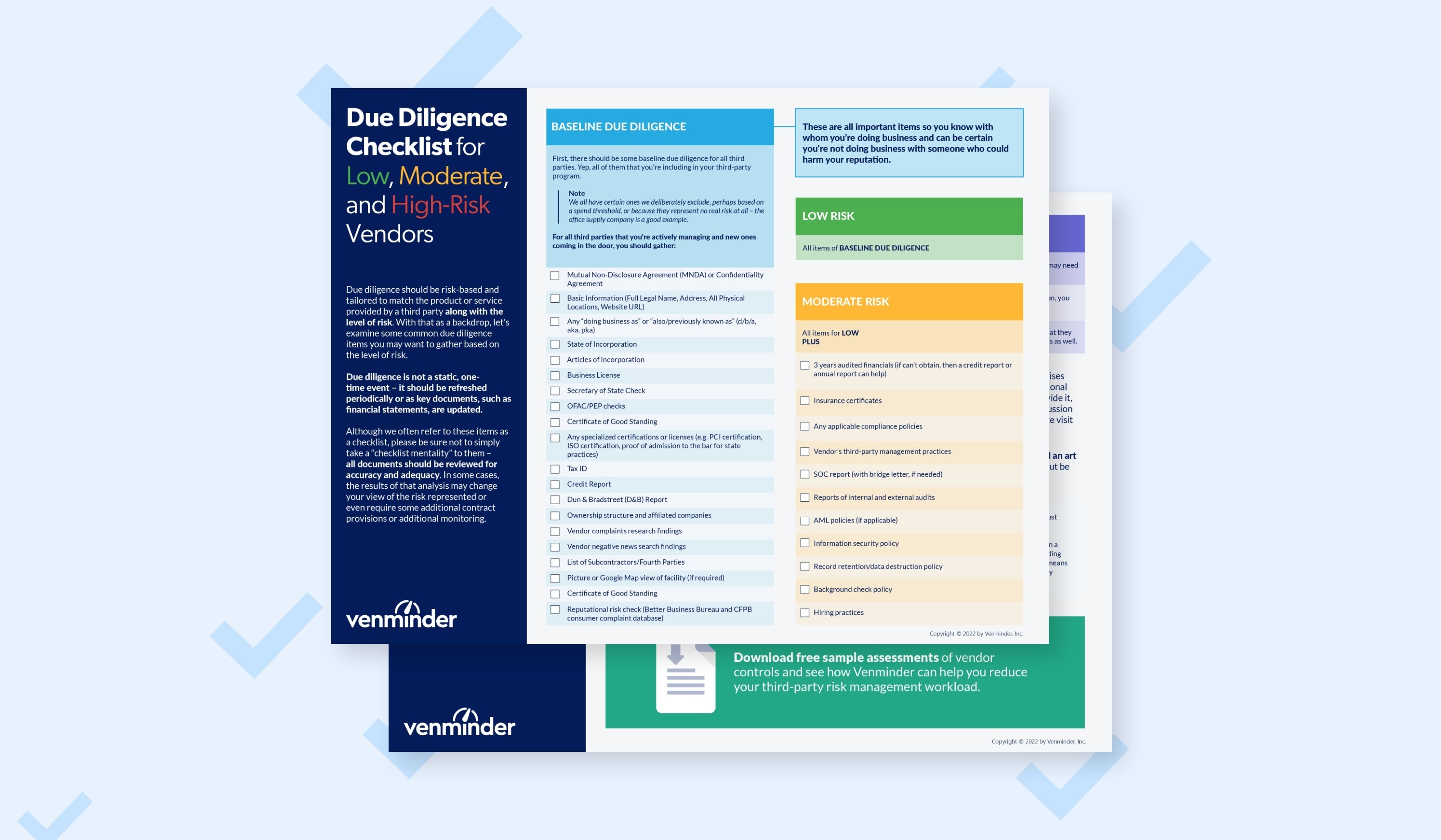
Use this checklist on specific common due diligence items you need to gather for based on if your vendor is classified as low, moderate or high risk.
due diligence checklist, high-risk vendor, checklist, vendor due diligence

Vendor risk management is a best practice, and, for many organizations, it's also a regulatory requirement. Dive deeper into the process of vendor risk management in this infographic.
vendor management process, vendor risk, risk management process,

Understanding what subservices (fourth parties) your vendors use is important. This infographic outlines how to review your subservice organizations within SOC reports.
subservice organizations, fourth-party vendor, reviewing SOC reports, vendor SOC report

Keeping the patient proactive care model in mind when considering TPRM is important. This podcast highlights 4 steps to take in creating a TPRM program for a health organization.
healthcare vendor management, proactive vendor management, third-party risk, health third-party risk
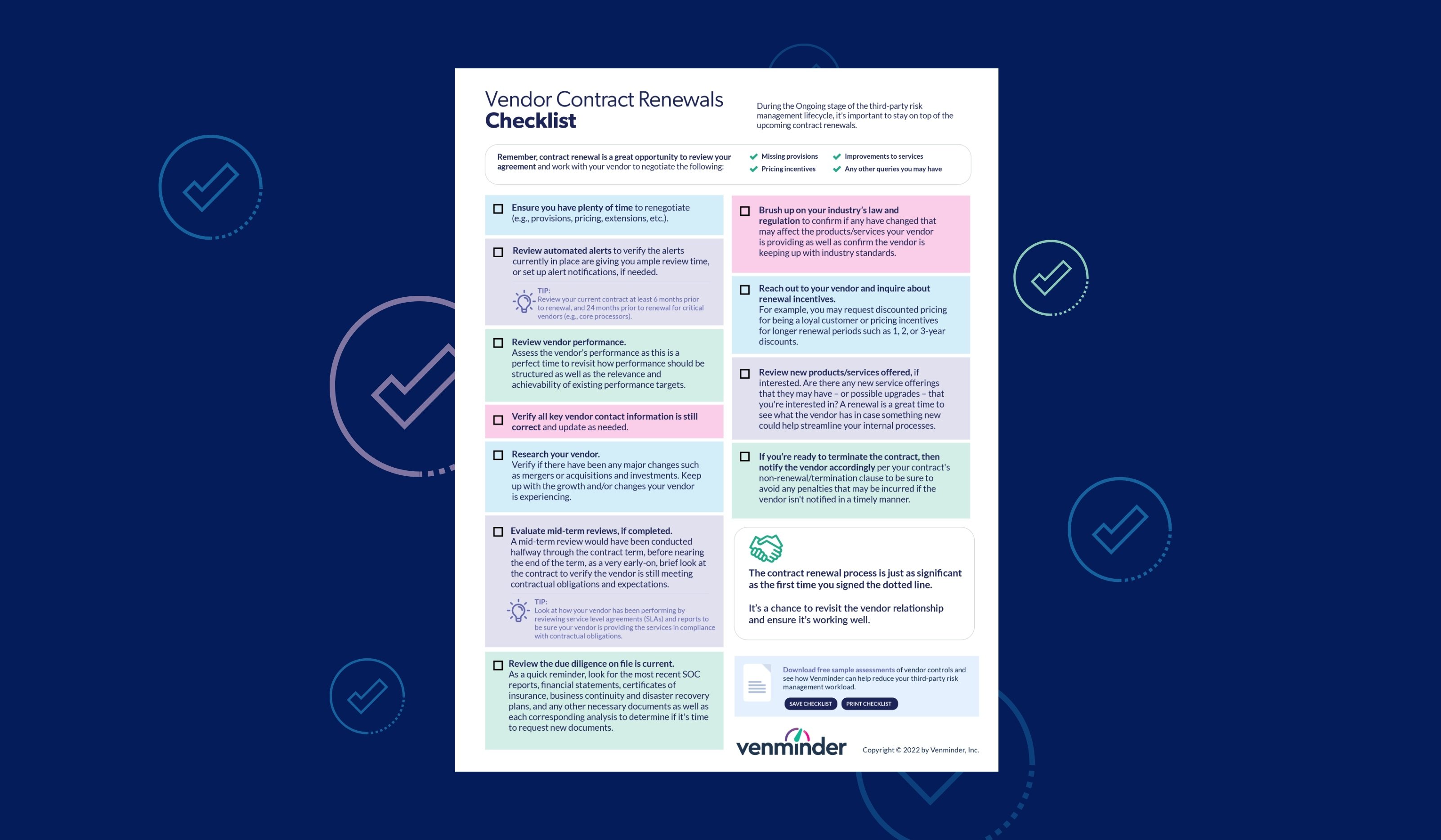
As a part of your ongoing monitoring, you need to stay on top of vendor contracts and renewal dates. Use this checklist to help.
contract management, vendor contracts, contract renewals, renewals
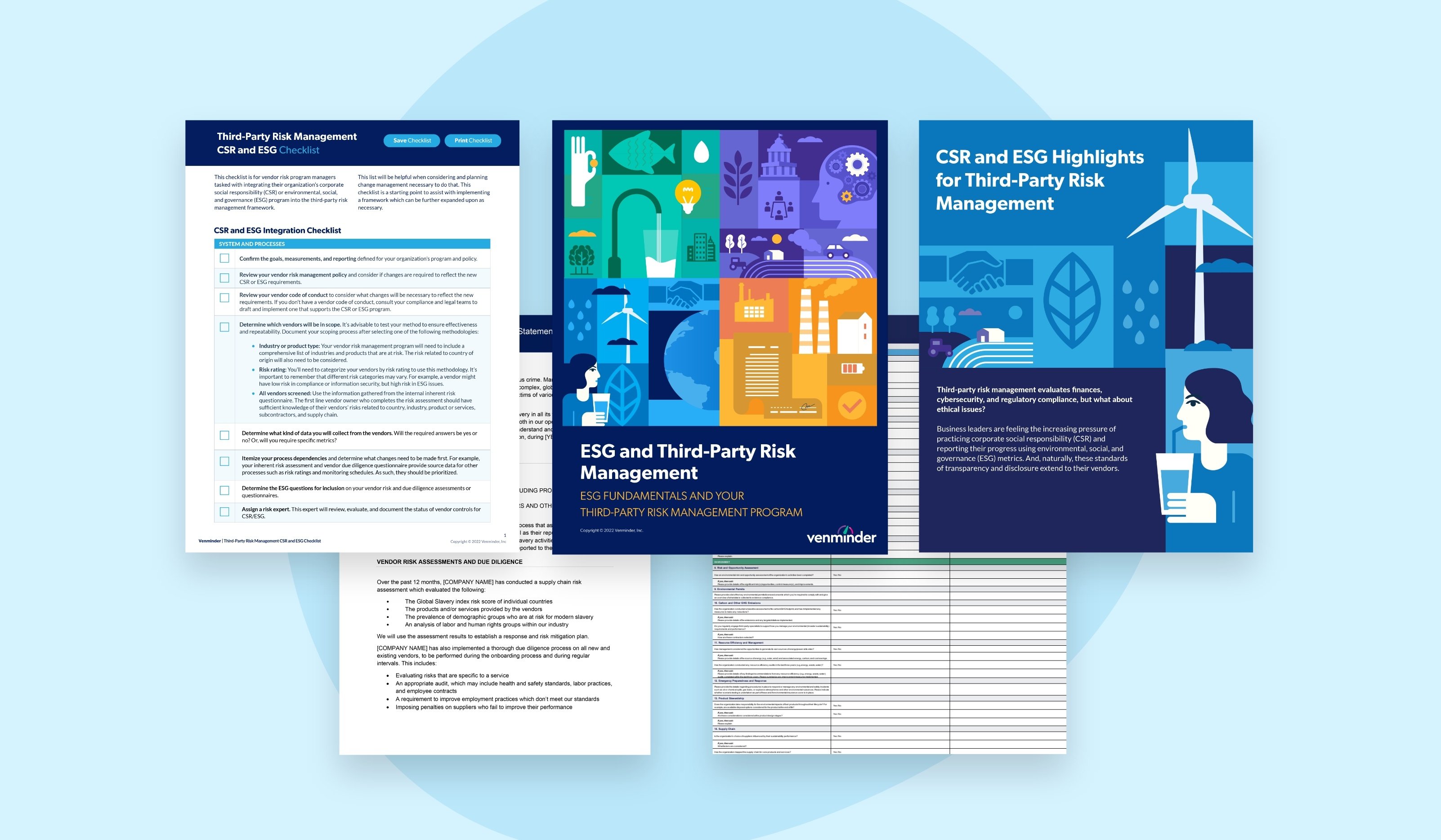
There is a lot to consider when incorporating CSR and ESG into current third-party risk management workflows and processes – including updates to your policy, risk assessments, due diligence, contracts, questionnaires and more.
third-party risk management, corporate social responsibility, environmental, social and governance, vendor management, toolkit

When managing vendor risk, many mistakenly consider critical and high risk synonymous, but they are not. There's an important difference between these terms and how they should be applied. Learn more in this infographic.
risk ratings, vendor criticality, high-risk vendor, vendor risk
There is still limited legislation on mandatory ESG disclosures, but regulators are continuing to address issues like climate change and modern slavery. Listen to this podcast to learn 3 ways to prepare your vendors.
esg disclosures, vendor esg, environmental, social and governance, regulations, disclosures
Ensure your organizations can balance the risks and rewards of the cloud by identifying the potential risks and thoroughly vetting your cloud service providers to make sure they meet your requirements.
cloud vendor, cloud service provider, cloud supplier, vendor management, considerations for cloud vendors
Use this handy checklist when thinking through the due diligence items you should be performing on your third parties.
vendor management, vendor risk management, check the box, document collection
Knowing how to conduct your vendor due diligence processes is only part of the equation. The real challenge for some organizations is understanding how to interpret and act on due diligence results. Learn how in this eBook.
vendor due diligence, due diligence collection, due diligence results, conducting vendor due diligence

No single financial statement will provide a full picture of a vendor's financial health. There are three statements that should be analyzed together to better understand financial risks posed.
financial statements, vendor financial health, financial performance, vendor financial statements

Measuring a vendor's performance is a necessary process that ensures the engagement continues to be beneficial. Also, helps protect your organization's reputation and ensures any issues are identified and addressed quickly.
measure vendor performance, vendor performance management, ways to measure, performance management

Has one of your critical healthcare vendors experienced a data breach? You can prepare now and anticipate you response to minimize damage, especially if that damage may involve your PHI or patient care.
patient care, healthcare data breach, healthcare organization, healthcare vendor management, vendor risk, cybersecurity

Having an exit strategy in case your vendor relationship must come to an end is crucial. Learn 4 exit strategies in this informational podcast.
vendor exit strategies, exit strategy, vendor management, contract management, terminate vendor

Knowing the risk your vendor brings to your organization is crucial. But, do you know and understand the risk categories or types to be reviewing and monitoring? Take the quiz to test how much you know!
quiz, risk categories, vendor management risk, vendor risk, third-party risk quiz

The healthcare industry practices proactive care, this same concept can be done for managing its third-party risks. Learn the importance for proactive vendor risk management in healthcare in this infographic.
healthcare, proactive care, proactive vendor risk management, vendor management, vendor risk, hipaa

Outsourcing a product or service to a vendor is a standard business strategy that can provide many benefits. Ensure you know these 6 vendor risk categories and common red flags.
red flags, outsourcing, risk categories, vendor management categories, vendor risk

The SEC released their 2022 Examination Priorities. Download this whitepaper to ensure your organization has your TPRM program in order.
exam preparation, vendor management exams, exam priorities, third-party risk management exam, cybersecurity, reports
Give yourself the ability to more successfully sidestep the aftermath of potentially disastrous scenarios by analyzing your vendor's business continuity and disaster recovery plans.
ongoing monitoring, disaster recover planning, business continuity planning, business planning, risk management

Vendor financial health includes many factors that your organization should be cognizant of and review accordingly. This podcast highlights three mistakes to avoid when reviewing.
vendor financial health, financial stability, financial reviews, vendor performance

The Standard Information Gathering (SIG) Lite questionnaire is a standardized questionnaire developed by Shared Assessments and used by organizations to provide information surrounding their control environment. Download a free SIG Lite assessment today.
sig lite, sig assessment, sig lite sample, free sig lite assessment
Vendor relationships can end for many reasons. Your organization's needs may have shifted and you're looking for a different vendor that better aligns with your goals. Whatever the reason for ending the relationship, you want to ensure you have an established offboarding process that minimizes issues.
offboarding, toolkit, comprehensive eBook, interactive checklist, vendor relationship management , exit strategy, termination

There is a beginning and end to every third-party relationship. In this podcast, you'll learn the stages of third-party risk management lifecycle.
lifecycle stages, onboarding, offboarding, ongoing activities, podcast

Learn the steps of the third-party risk management lifecycle to protect your organization from vendor risks using this toolkit.
third-party risk management lifecycle interactive toolkit PowerPoint Template Printable 1-Page PDF due diligence, contract management, risk assessment, scoping
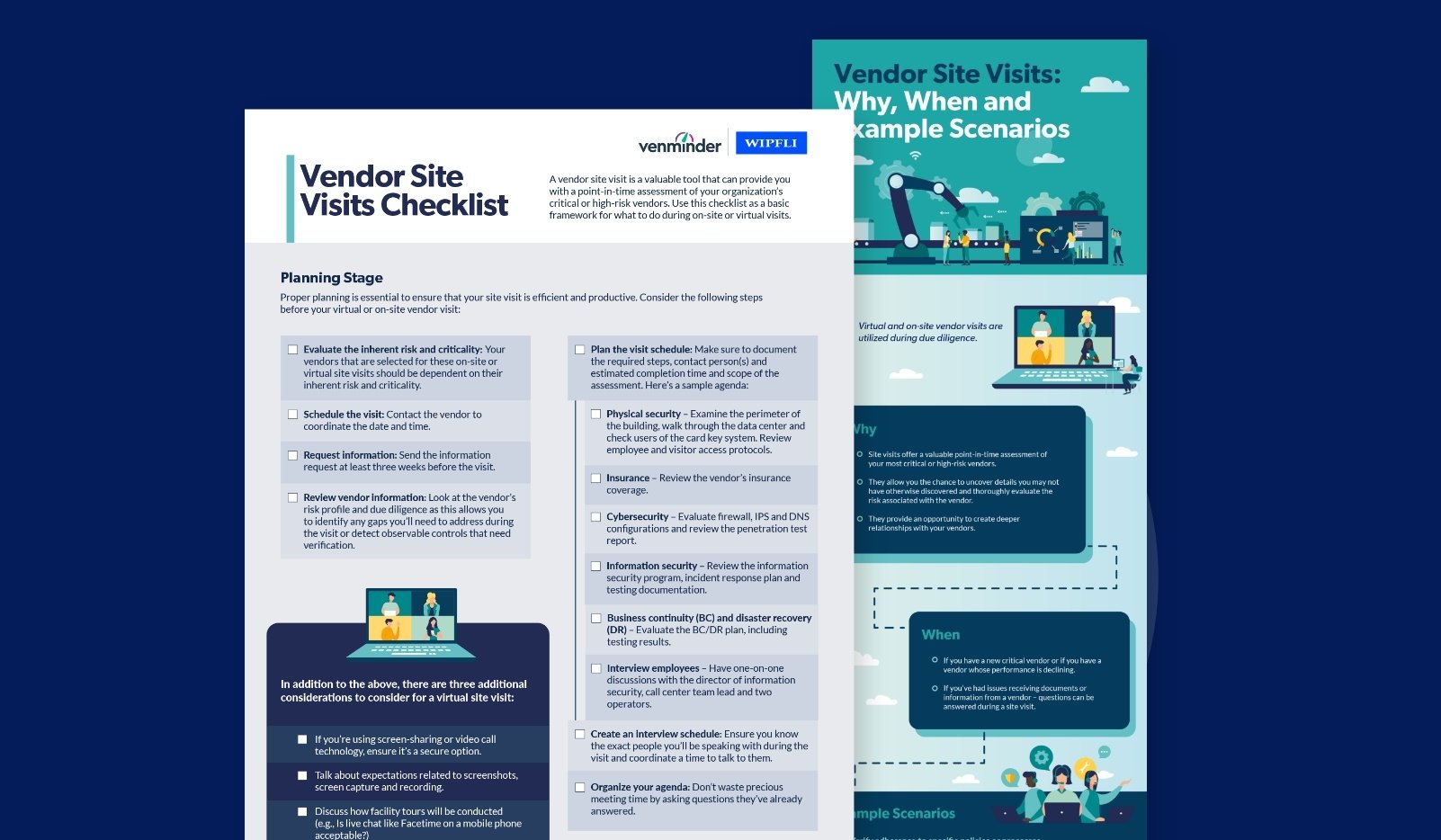
When your organization is exposed to a variety of vendor risks, it doesn't hurt to have the extra layer of protection that vendor site visits provide. Use this handy checklist and infographic to ensure your organization understands the importance of site visits.
checklist, on-site visit, virtual vendor visit, vendor risk

Not sure where to include in your vendor contracts? This eBook outlines sample contract language and recommended tips to help with contract creation.
contract management, vendor management, contract compliance, contract clauses
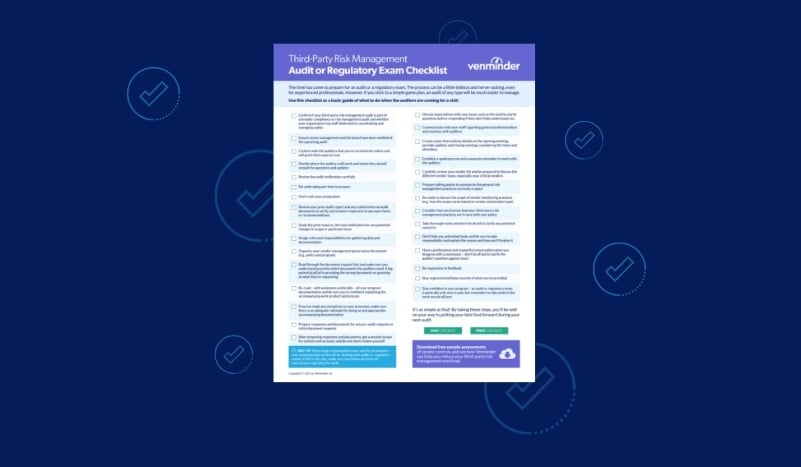
Use this checklist of things to help you manage and be sure you’re prepared when you have an upcoming audit or regulatory exam.
checklist, auditors, vendor management exam, vendor management audit
Although you don't have direct contact with your fourth parties, it's essential to understand how your third-party vendors manage their risk. Use this helpful infographic when discussing fourth-party due diligence with your vendors.
vendor relationship, vendor risk, vendor management, fourth-party risk
Successful vendor risk management requires the teamwork of stakeholders across the organization, and vendor managers play a crucial role. This eBook will help you engage, educate and enable your vendor managers.
vendor manager education, manager training, vendor manager tips, vendor management

Mitigating vendor risk is an important component of your vendor management program to ensure that your overall business operations can continue on. Listen to this podcast to learn how to mitigate vendor risk.
mitigate third-party risk, third-party risk mitigation, vendor risk management
Your third-party risk management program document lays out the concepts within the policy. Download this checklist to assist in creating an effective and mature third-party risk management document.
governance documentation, vendor management program document, policy documents, documentation

Your critical vendors provide products or services that your organization is highly dependent on. Learn the questions you can ask to determine if a vendor is critical or non-critical in this infographic.
high-risk vendor, vendor management, vendor risk, third-party vendor
Third-party risk management in practice is a complex ecosystem of processes, tasks, timing and risk mitigation. Various responsibilities and requirements are distributed across a range of accountable stakeholders. Download this toolkit for helpful templates and charts.
vendor management, vendor oversight, stakeholders, roles and responsibilities

Our annual State of Third-Party Risk Management survey highlighted four areas that are top concern for third-party risk management professionals this year. Listen on to learn them.
ESG, emerging risks, vendor management, due diligence

You should partner with a vendor who meets your organization’s expectations. Download this infographic for signs that it is time to end your vendor relationship.
vendor relationship, vendor management, third-party risk management, vendor profiling
Better understand when to start your due diligence, what to do if you can't get a document, why you need a good working relationship with your lines of business.
vendor management, third-party risk, document collection

All vendor relationships have inherent risks. If you choose to work with the vendor, you'll need different techniques to handle the risk. This infographic covers three risk handling techniques known as mitigation, transference and acceptance.
inherent risk, vendor relationship, vendor management

Third-party risk management is no exception, and as a practice, has steadily changed its tune over the past few decades. Explore the advances in third-party risk management in this infographic.
vendor management evolution, vendor lifecycle, industry change

2022 is going to be another year with a strong vendor management focus. Are you prepared? Listen to this podcast to learn 3 best practices to follow this year.
due diligence, vendor profiling, third-party risk management
As part of your vendor due diligence process and regardless of risk level, there are 19 items your organization should be committing to file for every third-party involved with your business.
initial vendor vetting, due diligence, onboarding

Listen to this podcast that highlights three main third-party risk management lessons learned in 2021. Learn how your organization can use these lessons to prepare for 2022.
due diligence, tips, vendor management
To help guide you and your team in understanding some of the most common terms found in a SOC report.
cybersecurity, information security, data breach

Well-written contracts are the foundation of the relationship between your organization and your vendor. Download this infographic to learn 5 reasons you should renegotiate vendor contracts.
vendor contract management, addendum, vendor relationship

Not sure where to start when building a third-party risk management program? This podcast covers 4 essentials tips to building a TPRM program and what you should include.
vendor management, due diligence, vendor risk

Don't let your vendors scare you this Halloween. Discover risky vendor situations that should be laid to rest in the third-party risk management cemetery in this infographic.
vendor management, vendor behavior, critical vendor, third-party risk management

Your third parties should be ranked as critical or non-critical for business disruption. This infographic outlines 10 general items that are needed to be on file for critical vendors.
vendor management, vendor risk, critical vendor management, due diligence, due diligence items to review

This infographic breaks down four key areas to pay attention to regarding vendor cybersecurity that will help you prepare your organization.
cybersecurity areas, vendor risk, vendor management

This podcast will highlight what you should be reviewing in your third-parties incident response plans. Gain an understanding of how your vendor will respond to an incident when it happens.
vendor management, third-party risk, continuity planning, vendor risk
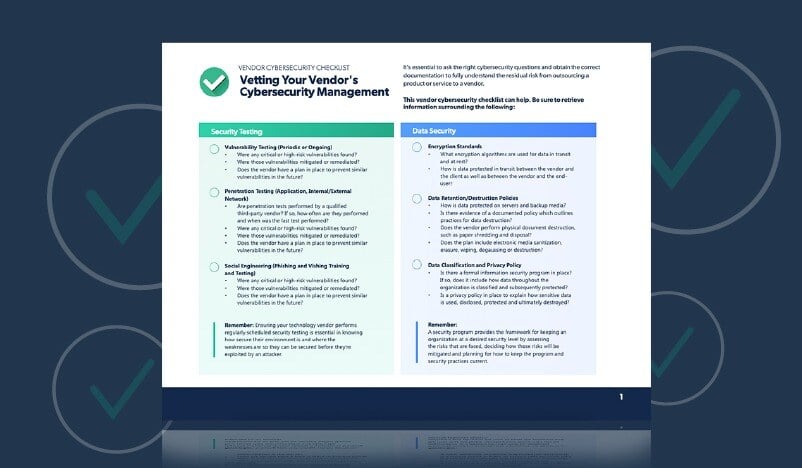
To help ensure you gather the information you need, use this handy checklist that covers what you need to review when analyzing your vendor’s cybersecurity.
data breach, information security, vendor cybersecurity checklist, cybersecurity checklist, checklist, vendor risk, cybersecurity risk

Michael Kossman, Chief Operating Officer and Chief Compliance Officer at Aspiriant, talks about the challenges of implementing a third-party risk program in asset management and the importance of third-party risk management.
third-party risk management program, due diligence, third-party risk challenges, vendor management
Timing is everything to be successful in vendor contract management. Download this guide to help get the most value from your vendor contracts during renewal time.
contract management, vendor management, contract guide
Clearly communicating setting expectations with your third party is essential for building a healthy and productive relationship. Download this playbook designed to support third-party risk management teams.
vendor relationships, prospective clients, communication, playbook for vendor managers

In this podcast, understand what a vendor confidentiality agreement is and how to create and review an agreement. Also, learn why these agreements are important in a third-party risk management strategy.
vendor risk, vendor management, NDA
Contract management is a key component in managing risk and vendor relationships. Our eBook is your tool to master vendor contract management.
contracts, third-party risk management, vendor contracts

Performing risk assessments may seem daunting, but are a worthwhile investment. Download this infographic to learn the tried-and-true steps to complete a vendor risk assessment.
vendor risk assessment, risk assessment, how-to, TPRM, vendor risk, risk management, vendor risk management, assessments, third-party risk
Vendor contracts work both as a roadmap to guide you through the business relationship and as a safety net. Download this eBook to learn what to include in critical vendor contracts.
critical vendors, critical vendor management, vendor contract management, vendor management

Understand how to get from inherent vendor risk to residual risk in this podcast. Learn the basics to calculate these risks.
vendor risk management, risk rating, calculating risk

Learn how to maximize value, cost, quality, day-to-day advantages and more. Download this infographic to understand the strategic advantages of doing TPRM.
Third-party risk management, cost advantage, quality advantage, maximize benefits, vendor management

Well-written business continuity and disaster recovery plans are important. Ensure your critical vendors are accounted for in your plans. Download the infographic to learn how.
third-party risk management, critical vendor management, continuity planning
Organizations are feeling the strain of keeping data and systems safe. Download this eBook to understand how TPRM and InfoSec teams can collaborate.
data, third-party vendors, relationship building, collaboration

Listen to this podcast to understand the various types of vendor business continuity and disaster recovery testing.
third-party risk management, testing, bc/dr testing, vendor management

Many of the OCIE's priorities changed as new risks emerged and existing risks were mitigated or heightened. Download the whitepaper to ensure you have your third-party risk management in order.
cybersecurity, vendor risk, third-party risk management, vendor management, ocie priorities
This eBook will guide you through creating an effective vendor risk assessment questionnaire of your own for proper third-party risk management.
vendor risk management, third-party risk management, questionnaires, assessments
Learn examples of fourth-party related clauses and how to write these requirements into your vendor contracts.
third-party risk management, due diligence, contract management, fourth parties, requirements
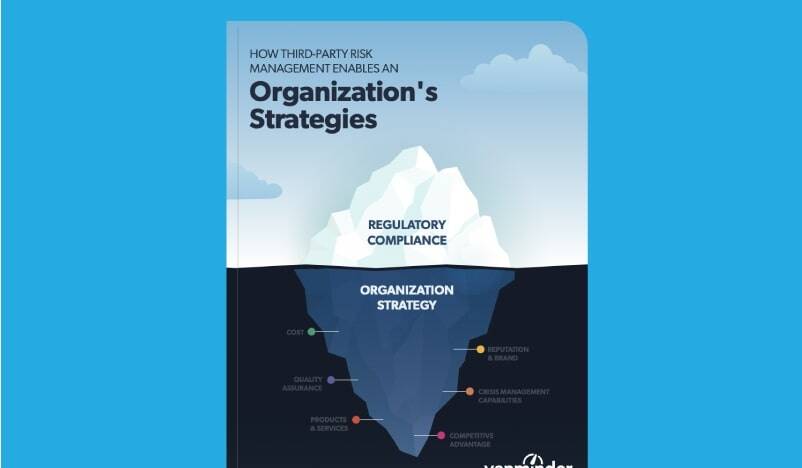
Realizing the value of third-party risk management as a strategic enabler requires you to look beyond the routine check-the-box requirements. Download the eBook to get an understanding on how TPRM can enable your organization's strategies.
vendor management, third-party risk management lifecycle, strategic enabler, regulatory compliance, organization strategy

Learn the most common myths of third-party risk management and learn the truth about the misconceptions in this infographic.
due diligence, vendor management, vendor risk

Understand the basis of vendor compliance risk and how to protect your organization from it in this podcast.
third-party risk management, risk assessment, risk category, due diligence

Download the infographic to learn the next steps to take that enhance your organizations internal processes and procedures.
financial risk, financial assessment
Understand the three core practices of third-party risk management in this podcast.
third-party risk management, vendor management, due diligence
It's essential to understand the risks posed in third-party relationships. Download this eBook to learn about the different types of vendor risk and how they can impact your operations.
due diligence, risk assessment, vendor risk, vendor management, financial risk, reputational risk, operational risk

Vendor financials are an important topic. Understand what documents are acceptable to ask for from privately held vendors in this podcast.
third-party risk management, vendor management, due diligence, document collection

Listen to this 90 second podcast to learn the three best practices for overseeing international vendors.
third-party risk management, risk assessment, risk category, due diligence, best practices, international vendors
Download this eBook to understand the importance of your vendor's financial health, especially your critical vendors and how they can affect your organizations reputation.
due diligence, risk assessment, vendor selection, financials
This extensive flight path assists with mastering third-party risk management. Successfully navigate through these third-party risk terminals to help your organization, your customers and your key stakeholders remain safe on the third-party risk trip.
due diligence, risk assessment, vendor selection

There are vendor management best practices you should be aware of to help avoid being deceived by a vendor. Listen to this podcast to quickly learn three tips to help you with the process.
vendor oversight, due diligence

This in-depth guide will walk you through the process of collecting due diligence and solutions for related common hurdles.
ongoing monitoring, oversight monitoring

Spring is the perfect time to dust off your vendor management program and clean up your processes with these tips.
vendor management, due diligence, policy

Play this interactive game and read the quick guide to learn why these 5 pitfalls of vendor risk come into play and what to do.
due diligence, vendor issues, third-party risk management, vendor risk

Listen to this 90-second podcast to hear more about the differences between questionnaires and assessments and why your organization needs both.
vendor assessments

Listen to this 90-second podcast to hear vendor due diligence fast facts you need to know to be successful.
due diligence

Listen to this 90-second podcast to hear more about how you can successfully offboard one of your vendors.
offboarding

This infographic will breakdown what you need to be looking for in your vendor's pandemic plan to keep your employees and customers safe.
business continuity, disaster recovery, pandemic planning, due diligence
Use this guide when developing, managing mature vendor management governance documentation.
ongoing monitoring
Listen to this week's podcast to help you create your third-party risk management procedures to be more successful.

Find out what you need to know about the process and the key points of ongoing vendor due diligence that you should be aware of in this 90-second podcast.
ongoing monitoring, oversight management
Learn 6 best practices you need to do when measuring, assessing and planning vendor management processes in the new year.

Are you selecting a core processing vendor? Listen to this 90-second podcast to learn about the factors you need to keep top of mind.
vendor vetting

Reputation vendor risk is every bit as important as other categories of risk, but it can be harder to gauge. This eBook will help you navigate it.
ongoing monitoring

New to third-party risk management? Understand what vendor management is and why it's important with this 90-second podcast.
vendor management, third-party risk management, best practices

View this interactive guide for how to review your vendor’s SOC reports by walking you through each section and the important areas to pay attention to.
cybersecurity

Find out what important lessons you need to be aware of going into the new year, so you can be more successful in vendor management.
vendor management

This podcast covers a few of the items that you should tackle before the end of the year to be better prepared for 2021.
vendor management

With the holiday season upon us, it’s time to determine if your vendors made the nice list! To help you, we’ve put together this checklist with what to consider.
vendor checklist, determine vendors, vendor due diligence

Whether you are new to vendor risk assessments, or want to improve your current approach, this video walks you through how to manage the process successfully.
risk assessment, risk rating
This video breaks down the basics of what vendor financial health is and why you should be including this step in your organization’s due diligence process.
oversight monitoring, ongoing monitoring

Listen to this podcast to help you figure out the best way to gather vendor management resources.
vendor management

Proper cybersecurity has never been more important than it is today. Use the six best practices covered in this video to help ensure your vendor can prevent, detect and respond to a cybersecurity issue.
data breach, information security

If you don’t have an adequate plan to properly manage your vendor’s risk, then your organization could be another scary statistic. Learn how to stay safe.
data breach, information security, data breach statistics

Listen to this week’s podcast for the top three benefits and ROI you can achieve by investing in third-party risk management.
vendor management

You can take proactive steps that will help you better protect your customers and reputation from a third-party data breach. Listen to this 90-second podcast for our top five tips.
data breach, cybersecurity, information security

To help fintechs win points with your clients, use this infographic that covers what you need to know about the changing vendor management expectations.
third-party risk management
In this podcast, learn the top four tips that will help fintech organizations more successfully meet their client and regulator expectations.
regulatory compliance

Learn about the importance of strong vendor information security and three best practices our experts recommend in this podcast.
data breach, cybersecurity

You can take specific steps that will help you maximize even the smallest budget for vendor management. Listen to this week’s podcast for the top three tips we recommend to help you make the most of your organization’s budget.

Use this quick, but comprehensive, guide to help mitigate fourth-party risk.

If you have well-developed vendor contracts, then you're setting your organization up for success when it comes to vendor oversight. Find out the top three reasons why your vendor contracts directly affect your level of oversight.
due diligence, contract management, ongoing monitoring

Chris Caputo, External Audit Coordinator at CMG Financial, shares his thoughts on commonly seen vendor management struggles and how to overcome them.
third-party risk management, due diligence

To help you better manage this stage in the vendor contract process, listen to this week’s 90-second podcast for the top tips our experts recommend.
contract management, contracts

Once you receive a vendor contract, there are specific steps that you should take for a more successful process. This 90-second podcast covers the 5 most important steps our experts recommend you're following.
contract management, contract negotiation
To make sure both your organization and your vendors are on the same page, follow the best practices covered in this infographic.
contract management, contract negotiation, contracts

Whether your exam is conducted in-person or remotely, this 90-second podcast covers the 7 most important items you should always have prepared.
examinations
Understand the quality of your cloud vendor's control environment. Our CAIQ Assessment will show you if there's sufficient confidentiality, availability and integrity in key areas.

Jenn Wilkinson, Vice President of Strategic Vendor Management at Cenlar FSB, shares her thoughts on the process of building an expert vendor management program from the ground up.
third-party risk management program, due diligence, initial vendor vetting
This comprehensive eBook breaks down how to create your third-party risk management procedures documentation.
vendor risk management program

By not being aware of the hazards of incomplete vendor due diligence, you could be putting your organization at risk. Listen to this 90-second podcast for the most important hazards to know.
ongoing monitoring, oversight management

This infographic will walk you through key best practices and a process that will help you mitigate some of the risks of dealing with issues with your vendors.
issue management, vendor issues, vendor issue management

Listen to this week’s podcast to find out three important questions we recommend you include in your questionnaire.
cybersecurity

Understand the basics of business continuity management with this 90-second podcast that breaks down what you need to know about the process.
BCP

When it comes to vendor risk assessments, the process can seem overwhelming. This infographic helps you determine your vendor's risk rating.
rate vendor risk, risk rating, vendor risk ratings
There are important requests you need to include in all of your vendor contract negotiations. These 5 will help set your organization up for success. Find out what they are by listening to this podcast.

Looking for ways to improve your program in light of the recent pandemic? This infographic breaks down what you need to know.
covid 19, third-party risk management covid, covid 19 tprm, pandemic third-party risk management

With COVID-19 impacting many vendors' businesses, use this infographic to help you prepare for the aftermath.

Listen this roundtable discussion to hear from three third-party risk management experts as they share their thoughts on handling problem vendors who won't play nice in the sandbox.
ongoing monitoring, oversight, due diligence

Do you know what steps to take after the vendor management exam concludes? This infographic breaks down the main areas that you should focus on.
examinations, vendor management exam, vendor exams

Organizations may not have the internal capabilities to properly manage every step of the process. Listen to this podcast to learn how to determine if your organization could benefit from outsourcing vendor management support.
staffing, outsourcing

You should be proactively taking steps to mitigate risks posed by potentially vulnerable vendors. This podcast covers seven steps you can take to ensure your organization is safe against vulnerable vendors.
ongoing monitoring, oversight, due diligence, oversight management

You must maintain proper vendor oversight, especially in today's changing environment. Download this infographic that breaks down how to handle the process efficiently.
ongoing monitoring, oversight, due diligence, vendor oversight tips

There are three key components of information security that you should monitor when analyzing your vendor’s information security strength. Listen to this podcast to understand the CIA Triad.
cybersecurity, information security
Protect your organization by looking out for the 10 signs covered in this 90-second podcast that will indicate your vendor's financial performance is declining.
financials

There will be business events that occur with your vendor that can impact your organization. Listen to this 90-second podcast to learn 11 items to look for in business continuity plans.

Use the 11 tips in this infographic to help you prepare yourself for properly managing vendor risk.
third-party risk, third-party risk management, vendor management

Is your vendor’s financial performance declining? To protect your organization there are some warning signs to look out for. Be aware of what the consequences are and your steps for recourse.
oversight, ongoing monitoring

There are 3 "behind the scenes" vendor lifecycle requirements that are constant and should be maintained throughout the entire vendor relationship. Listen to this week's 90-second podcast to learn more about what they are and why.
third-party risk management

These COVID-19 vendor management best practices will help you with current challenges.
third-party risk best practices

While preparing for a vendor management exam is a crucial step in the process, how you follow-up after the exam is equally as important. Listen to this podcast that will cover the 5 next steps you should be taking after a vendor management exam concludes.
examination, third-party exam, audit

By periodically conducting due diligence, you will be able to ensure your vendors are still meeting your organization’s needs. This 90-second podcast covers 4 tips that will help get you started.

Regulatory guidance sets out fundamental expectations. It’s important from the management and exam standpoint that these pillars are in place. Learn more in this podcast.

Communication and collaboration are key in implementing a risk assessment process. Download this infographic for how to collaborate during the process.
vendor risk assessments, risk assessments, collaborate vendor risk assessment process

Does your organization understand your vendor’s financial viability and performance? Here are 4 reasons why your vendor’s financial performance is crucial for you to report on.

Due diligence is an important step in vendor management, so cutting corners can be dangerous. Learn what could go wrong with a check-the-box approach.
Performing vendor due diligence is a regulatory requirement and sound business practice. This eBook helps you identify unacceptable vendor due diligence in 5 major reports.
vendor due diligence, unacceptable vendor due diligence, bad due diligence

Vendor risk management is important to meet regulatory guidelines. Listen to this podcast for 4 tips to help you make third-party risk a key priority in your organization.

Do you need help determining what your vendor risk appetite is? This podcast answers common questions you may have when it comes to determining your organization’s risk appetite.

Your vendor management program should be specific and unique to your organization’s needs. Listen to the 6 best practices covered in this podcast for creating a third-party risk program.

This podcast breaks down what initial vendor due diligence is and why your organization should incorporate it into your vendor management program.

Do you know the signs of an inadequate vendor management program? Download this eBook to walk you through what you need to look out for.
vendor management program, bad vendor management, signs of bad vendor management

Different types of vendor risk require unique approaches. This podcast breaks down the 6 main categories of vendor risk to help you improve your organization's overall approach.

Join us and Glen Trudel, Partner at Ballard Spahr, LLC. We discuss the biggest third-party risk struggles financial institutions face today, how to handle ongoing vendor risk management and vendor oversight, addressing cybersecurity, board involvement, industry expectations and more.

Each vendor management concept brings varying components to an organization’s overall structure. Listen to this podcast to dive deeper into each concept.

When your vendor fails to meet the SLA requirements outlined in your contract, it can have negative consequences. Listen to this podcast for next steps.

If your vendor isn't meeting your organization’s needs, it may be time to start searching for a new vendor. Listen to this podcast for steps to help you with the process.

Use the third-party risk lessons and guidance learned this year to help your organization be even more successful with vendor management in 2020.

Listen to this 90-second podcast to hear our four third-party risk expert tips to help you when improving your vendor due diligence strategy.
Here are examples of vendor management horror stories so you know what to avoid in order to better protect your organization.

There are many benefits of vendor risk management. Understand why vendor risk is important and how to use these steps in your organization by listening to this podcast.

Budget season is upon us! Prepare yourself and your organization by planning ahead now for third-party risk. Listen to this podcast for more information.

To help you with the due diligence and vendor oversight stages of the third-party risk process, use this infographic to help walk you through what you need to know.
ongoing monitoring

Understand why the risk your third parties pose to you is important to your financial institution clients. Download the infographic.
fintech provider, financial institution
You can start to better understanding of what specific items you need to look for in your vendor’s cybersecurity plan with this 90-second podcast.
You need to focus on oversight and ongoing monitoring of your vendors before and after you sign the contract using the 6 ways to improve your process.

This useful infographic that will walk you through what to negotiate into a contract for third-party management.

Proper vendor management requires you to periodically go update and improve elements of your program. Listen to this 90-second podcast to hear specific steps to take to improve your third-party risk program.
vendor management program, vendor risk management program

There are steps you can take to make the process more efficient when reviewing a SOC report. Listen to this week’s podcast to find out 7 steps to take.
It's critical to verify if your vendor is implementing strong business continuity and disaster recovery planning. This eBook will break it down for you.

The constant shift can lead to occasional problems in third-party risk management. If you take the time to manage the process correctly and implement specific procedures, it could help you avoid costly errors down the line.
ongoing monitoring, oversight, due diligence, issue management

In this infographic, dive into the negotiation component and ensure maximum value from your outsourced relationship.
Regulatory risk is used to determine the vendor relationship’s risk rating . Listen to this 90-second podcast to learn more about the categories of regulatory risk and how you can determine your vendors' regulatory risk.

Improving how your organization manages the process will help you clearly define vendor expectations and responsibilities. Watch this 90-second video to get a fast overview and best practices for vendor contract management.
Because there's no one-size-fits all approach to vendor management, it's important you determine which model will help your organization reach its goals. This eBook will help.

For a smooth third-party risk examination, 3-4 months in advance of the examiners’ arrival you should prepare or fine-tune these 9 documentation items. We'll tell you what they are and some tips.
exams

Jo Ann Barefoot, CEO at Barefoot Innovation group and Cofounder at Hummingbird Regtech, shares her thought provoking insight on how organizations are handling third-party risk management.
regtech

This interview features Michael Donnella, Corporate Compliance Officer of Murphy Oil Corporation. Michael shares his perspective on corporate compliance and why having a culture of compliance in third-party management is crucial for organizations.
regulatory compliance, regulatory guidance

Throughout your vendor risk management process, you should be conducting due diligence both pre and post-contract. In this 90-second video, learn the different due diligence items you should be requesting from your third-party vendors.
contract management

You need to also monitor your vendor's complaints as a critical part of third-party risk management. Listen to this podcast for more information.

Determining who your critical vendors are is an important part of the process. Watch this 90-second video, and hear important questions to ask yourself in order to figure out which of your vendors are critical.
risk assessments

Improve your vendor due diligence process, with this informative infographic that covers specific strategies that you can use to protect your organization.

With 2019 underway, we decided to put together some tips to help your organization stay proactive in vendor management. This podcast will give you a quick refresher on third-party risk best practices.

An effective third-party risk management program is key to protecting your organization. Watch this 90-second video to learn the 9 steps that you should take in order to create a third-party risk program.

To help you and your team succeed in your vendor management, we’ve put together an infographic on the top 10 best practices that every good vendor manager should follow.

Listen to this interview to hear President and CEO of Argos Risk, Lori Frank, cover current third-party risk management challenges and shifts in ongoing monitoring trends in the industry today.
oversight management
Download this educational eBook to learn how to impress auditors and requirements to be more prepared for your next vendor risk exam.

How your organization manages and responds to complaints has become critical. Here are some tips to help you develop an effective complaint management system.

Risk assessments are vital to the success of an organization’s vendor management program as you delve further into any risks vendors pose. This infographic shows you the what, why, when, who and where of them.

Here are some specific steps you can take with fourth party risk management that will help be more prepared and protect your organization.

Having a strong vendor risk management program is a great way to protect you and your customers. This infographic covers how to create a program.

Due diligence is another term for third-party document collection. It is one of the most critical activities in third-party risk management. Watch this quick overview of best practices for third-party document collection.

Listen to this podcast for 5 important steps that you can take to measure your vendor's financial health.

Listen to this podcast to learn about vendor contract management from our experts, the importance of contracts to your organization and what steps you should take to protect your institution.
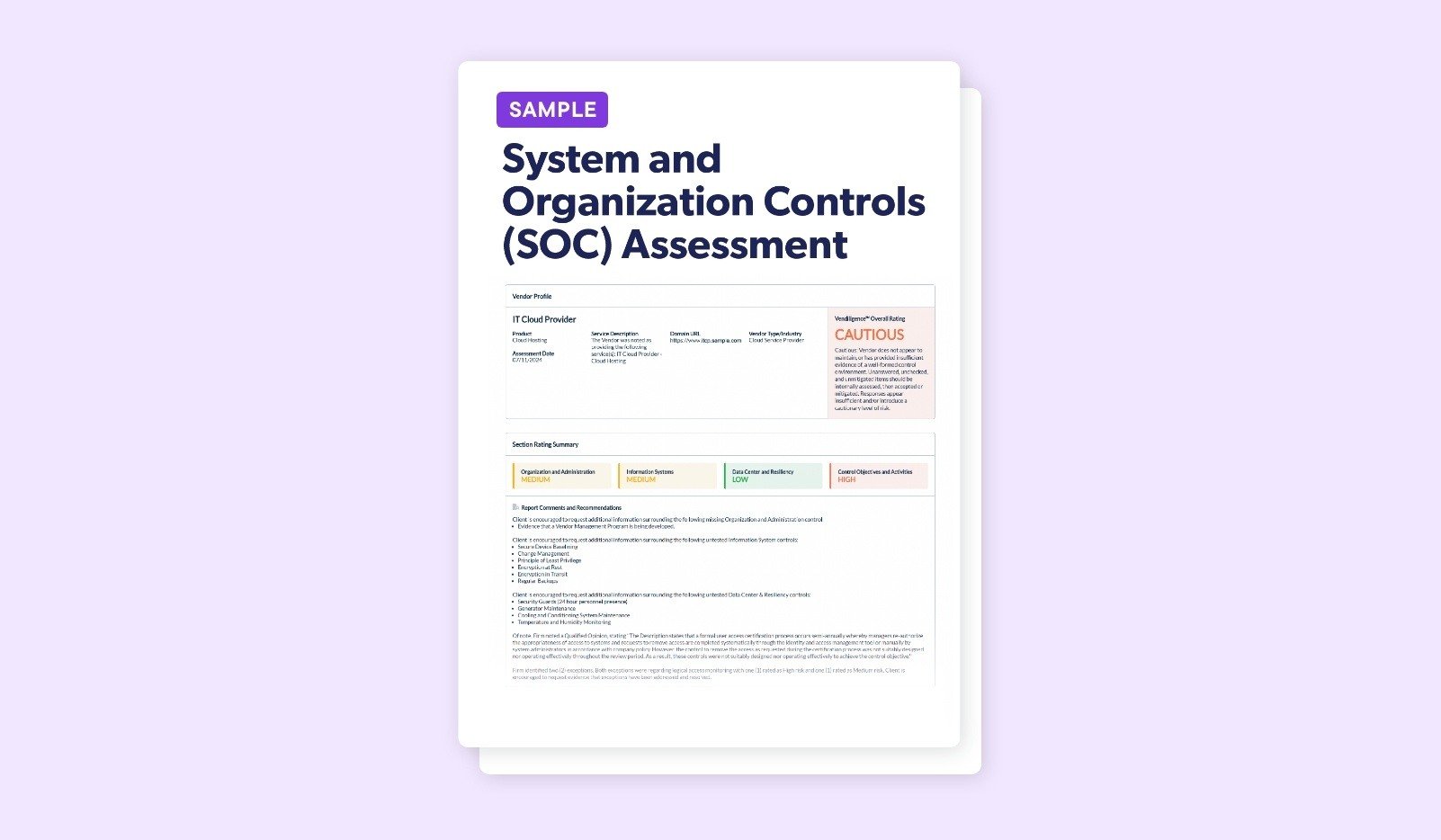
Download a sample SOC analysis summary document that allows you to focus on the important components, including the set of controls that you control directly.
cybersecurity, information security

Is there a way to know if you have “dirty” vendors who could use some dusting off? Ensure you know everything important and what steps to take to help you spring clean your vendors.

This interview features Jennie Fowler, Director of EPMO and Vendor Management Officer, at American Credit Acceptance. Throughout the interview, Jennie shares her recommendations to obtain support from the C-suite when it comes to vendor management.
regulatory guidance, buy-in, reporting

Do you know who your fourth parties are? This infographic will help get you started with the when and how of identifying your fourth-party vendors.
fourth-party management, fourth-party vendors, fourth-party vendor risk

In this 90-second podcast, we will cover the specific steps you should take in order to determine the vendors that need to be included in your vendor oversight.

This interview focuses on the three lines of defense model discussion and how there should be a well-developed vendor management structure at all organizations regardless of the size.
information security
Download this eBook for the challenges and possible solutions you may potentially encounter to help you prepare for various vendor management issues.

Maintaining strong vendor management relationships will help lead to a successful partnership for your organization. In today’s podcast, we’ll cover 8 important tips to maintain good vendor relationships in 90 seconds.

UDAAP has presented some concern to third-party risk professionals. In this podcast we cover procedures and best practices to effectively manage UDAAP and your third parties.
regulatory compliance, guidance
With the increase in regulations and vendor oversight requirements, managing vendors with a spreadsheet is very inefficient. Here are 7 reasons why spreadsheets will not cut it anymore.
reporting, regtech

This interview focuses on the role of vendor management in financial institutions from a legal and regulatory perspective. We cover the pain points organizations are experiencing for third-party risk, which includes data aggregation, organizational consistency, reporting and cybersecurity.

We'll cover tips for developing a vendor risk assessment template, also referred to as a VRA questionnaire. These are important while assessing how much risk your vendor presents to you. Check out our 5 recommendations.

When getting started in vendor management, there are three sets of documents that you want to create. The first document that you should focus on writing is your third-party risk policy. In this podcast, we're going to walk you through 6 steps to take in order to write an effective policy.

What is inherent risk and how to determine it, why residual risk is never higher than inherent risk and 4 important tips to follow.
inherent vendor risk, residual vendor risk, inherent vs residual risk

Evaluating your vendor's regulatory risks ahead of time can help you avoid some very costly surprises down the road. Use this infographic to see how to rate your vendor's regulatory risks.
regulatory risk, vendor regulatory risk, rate vendor risk, rate vendor regulatory risks

Are you looking to expand your vendor management team? There are certain steps you can take in order to find the most effective team your organization. In this podcast, we discuss 5 tips to recruit potential vendor management team candidates.
staffing
Put your knowledge to the test by downloading this crossword puzzle that is filled with third-party risk clues and phrases.

Vendor management typically takes an individual who is meticulous in detail, thorough and patient to perform the job. In this podcast, we’ll wrap up the year and touch on some attributes found in good vendor managers.
staffing
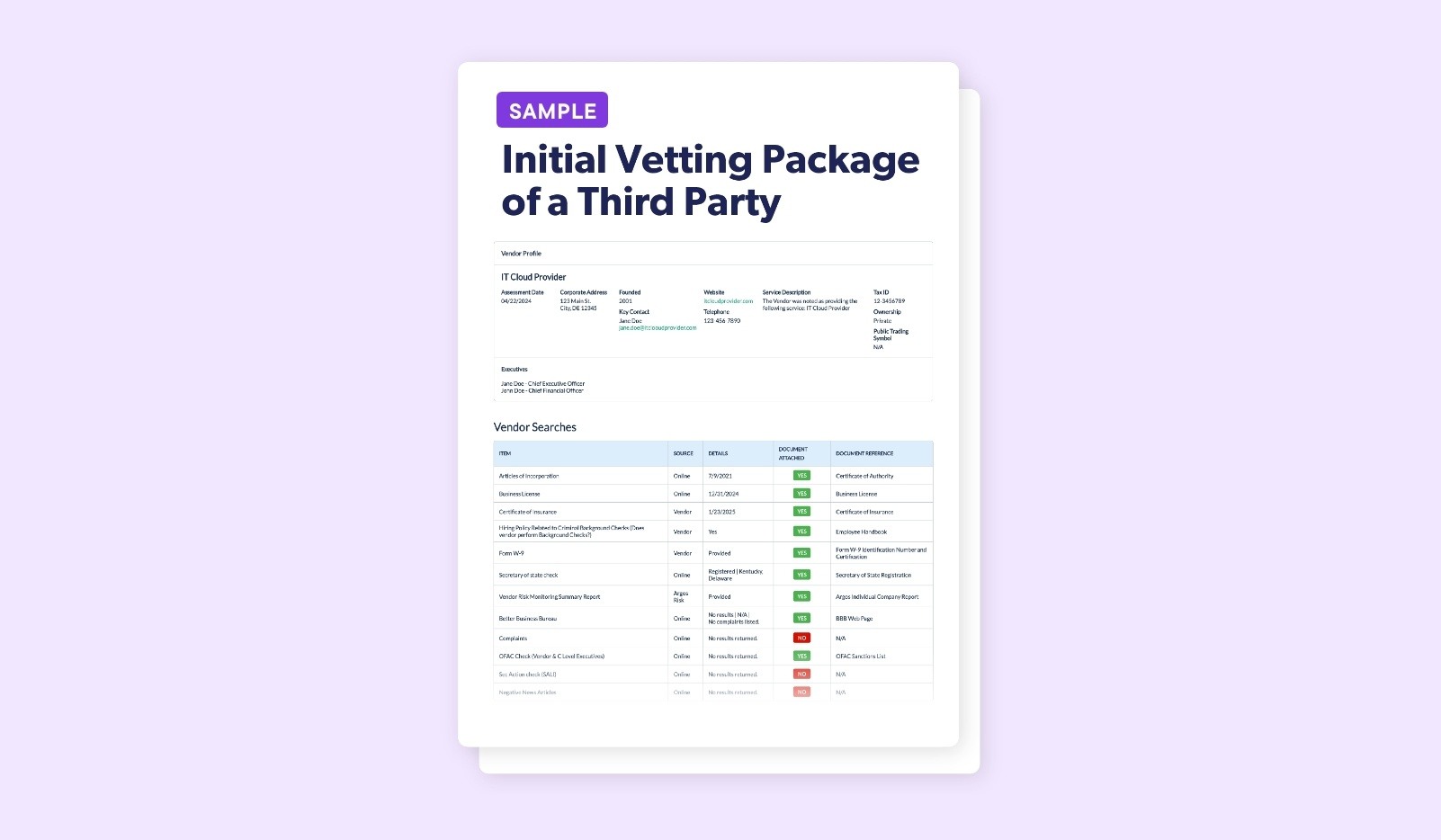
In every new relationship should be doing the necessary research to know your vendor and meet regulatory requirements. This assessment shows you how to do the research.
This interview covers qualifications that are needed on a third-party risk management team, why cybersecurity risk is something that you can never defeat and a thought provoking conundrum about the introduction of decentralized technology.
cybersecurity, team

It's easy to get so involved with vendor management that you miss basic, but key, items. Find out what the top 25 errors are to avoid in your vendor management program in 2019.
risk management errors, how to avoid vrm errors, vendor risk management, third-party risk errors

This podcast covers 7 of the 2018 best practices that you should continue into the new year. They range from engaging the first line of defense through continuing education.
third-party risk management process

Now is the time to reflect on the year and some of those reasons to be thankful for a well-developed vendor management program. Let's go through 10 reasons now.

This interview covers both a legal and industry perspective on third-party risk, impact of fraud in third-party risk management, discussion regarding increased oversight at the state level and a post Dodd-Frank Act lesson - senior management and the board must be involved.
regulatory compliance, guidance, reporting

Third-party risk management needs to be a part of the board's regular activities. Listen to our 5 tips to help you prepare for periodic vendor updates to the board

This infographic will guide you through what you need to know about UDAAP and add clarity to what to do as it relates to your vendors.
udaap, vendors udaap, udaap vendors, what is udaap

With the increase in regulatory demands, it's crucial to be as efficient as possible. Take the right steps to increase efficiency - we have 8.
third-party risk efficiency, improve third-party risk management, vendor management improvement, program improvement

We gathered 8 terrifying real-life third-party risk management stories from compliance officers and vendor management teams across various sizes of organizations. Learn from their mistakes.
third-party risk management stories, tprm stories, vendor management stories

Be prepared for when your vendor experiences a data breach by doing these 10 best practices. Hackers do not discriminate when looking for an asset to attack.
handle vendor data breach, vendor data breach, how to handle vendor data breach, vendor data breach best practices
Follow these basic dos and don'ts of vendor contract risk management. There are steps to take, 8 additional tips to help mitigate vendor risk and 5 huge mistakes to avoid.
vendor contract, contract management, vendor contract management process

Join us and Ashley Kelley, VP of ERM at APCU, for a discussion on third-party risk overall, centralizing third-party risk management - why it can be a struggle but is needed, insight from the VP for the International Association of Financial Crimes Investigators (IAFCI) on cybersecurity expectations and concerns and more.

A well-developed policy, program and procedure documents are all crucial to the success of an organization’s third-party risk management department. Listen for some quick tips to help you.
vendor management program

Could your vendors be your weak link? To learn how to protect your organization from third-party vendor cyber risk, our infographic covers 7 key steps to follow.
cybersecurity, information security, rising vendor risk

SOC reports differ based on what they cover, how the auditor performs the assessment and what level of detail the reports include. Learn the differences between a vendor SOC 1 and SOC 2 report and Type 1 and Type 2.
cybersecurity, information security

Fourth parties are just as important as third parties. They can have access to your confidential information and thus you must make sure you do proper oversight and effort with these companies.
fourth-party vendor, fourth-party vendor oversight, vendor oversight

Join Venminder and Amy Hanna Keeney, Attorney with Adams and Reese LLP, for a thought-provoking interview on 2018 CFPB progress & activities, what you can expect from the CFPB in regards to regulatory guidance, the future of UDAAP enforcement actions, CFPB hot topics for the coming months and more.
regulatory guidance, regulatory compliance
Whether negotiating a new vendor relationship or renewing an existing one, learn how to develop a contract that clearly defines expectations and responsibilities of the vendor, tips and best practices.
vendor contract, contract management, sign vendor contract

In this podcast, we'll go through 11 reasons to consider your third-party risk management department/program when budgeting for the upcoming year.
budget, ROI

Join us and Michael Morris, Systems Partner at Porter Keadle Moore, LLP, for an auditor's perspective on vendor risk management. Topics covered include: best practices for managing risk, addressing today's cybersecurity threats and risks, top areas of concern for a SOC audit report and more.
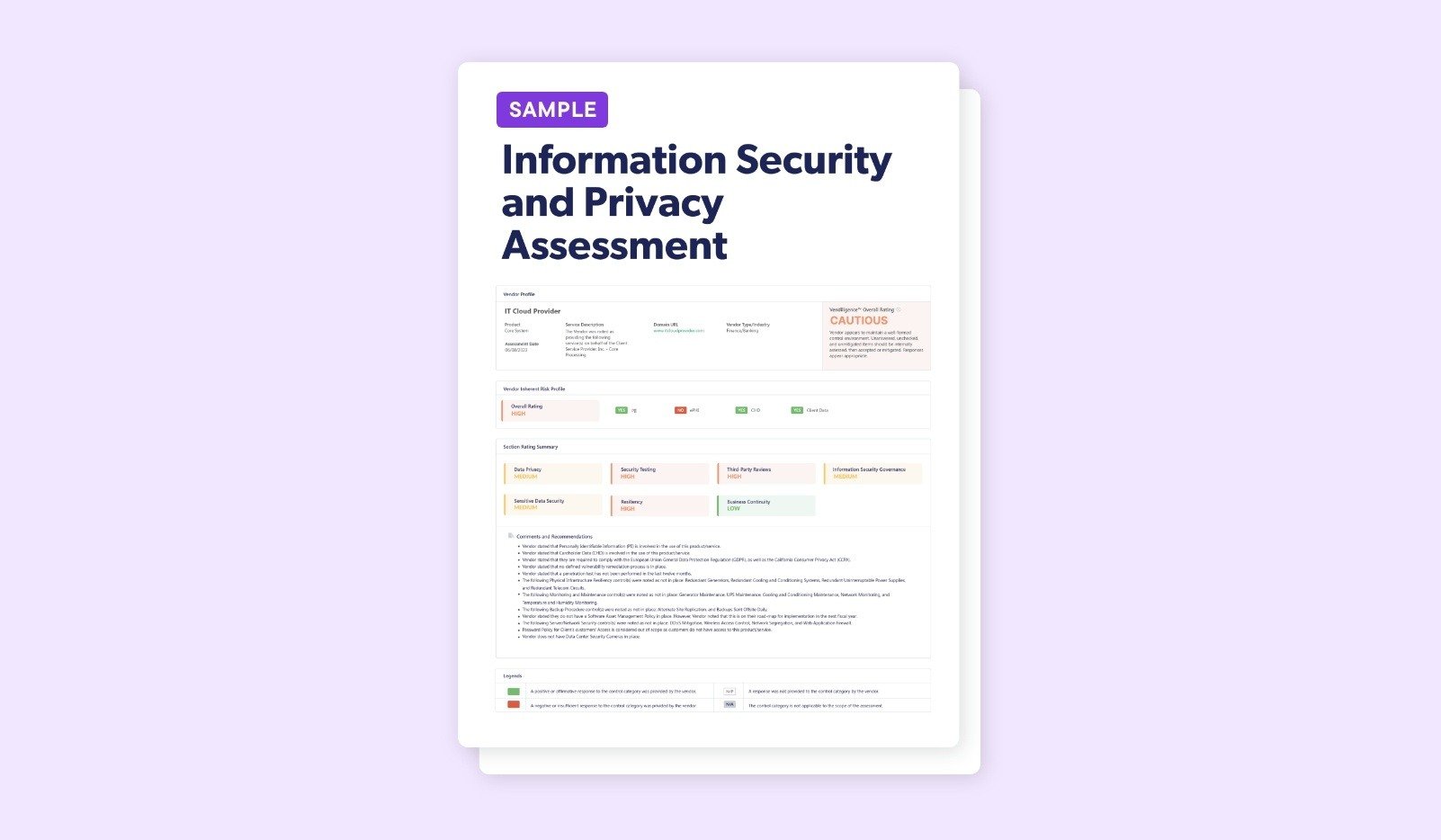
This information security and privacy assessment that covers key cybersecurity and information security risks that can help identify areas of possible weaknesses.

It's a best practice to consider the costs associated with negotiating key contract terms and pricing within your third-party risk management program. Listen to this podcast that covers 5 vendor contract considerations for your budget.
ROI

This podcast covers how FIEC’s Appendix J relates to your vendor risk management program and 4 key elements of business continuity planning that you should address when contracting with a third-party service provider.
regulatory guidance, compliance

Learn what to include, reasons why you'd need multiple assessments, an example and 3 best practices.
assess vendors, product level assessment, how to assess vendors

Take a look at what we consider to be 24 of the current best practices to minimize vendor risk and ensure your org is a top performer in TPRM.
minimize vendor risk, how to minimize vendor risk, best practices to mitigate risk, mitigate vendor risk

Allow your clients to feel much more at ease when selecting you as their preferred vendor of choice to continue doing business with - follow these 5 best practices now for a well-developed and organized third-party risk management process.

Ensuring that your vendors are meeting their regulatory exam expectations is a key part of vendor risk management. Download this infographic now to learn about managing and mitigating compliance risk.
vendor compliance, know your vendor

Vendor vetting and ongoing monitoring are both important stages of the vendor lifecycle and due diligence process, but, why exactly is due diligence so important for vendor risk management? Listen to our third-party risk management podcast now to learn the top 5 reasons.

When and how to request a SOC for Cybersecurity, what it includes and differences between a SOC 2 vs. a SOC for Cybersecurity. Mitigate cybersecurity risk now.
vendor soc report, soc for cybersecurity, cybersecurity soc report
As a third-party service provider, the SSAE 18 audit requires that you have an effective vendor management program in place. Are you prepared? In our latest eBook, we'll take you through all the steps you need to know for..
regulatory compliance, regulatory guidance, ssae 18, ssae 18 audit

We all hope to never experience a breach at our organization, but if it does happen, do you know what to do? You can minimize the chance of it happening again by using these 4 best practices to improve your third-party risk management program.
data breach, cybersecurity, information security

What the SLA should state, opportunities provided by SLAs to your organization, negotiating service levels, the 8 elements a model SLA should include, best practices and more.
exit strategy, get out of vendor contract, vendor contracts, contract management

Third-party risk management is associated with a great deal of tasks and a large workload, so here are 6 tips that can provide some relief.
On-site visits are an important part of vendor due diligence. While the vendor types which warrant one will vary, these tried and true best practices remain the same.
vendor on-site visits, best practices site visits
Proper vendor contract management can mitigate risk. Learn the phases of contract management, how to overcome challenges and best practices.
contract management, vendor contract management, vendor contracts

Listen to this third-party risk management podcast where we take into consideration regulatory guidance OCC Bulletins 2013-29 and 2017-7 and FDIC Letter 44-2008 to help guide you through the vendor risk assessment process. Learn how to complete a vendor risk assessment, steps and tips.

A third-party information security assessment is an integral part of judging a vendor's risk level. Learn 3 core principles, key regulatory guidance, why use one and 3 questions to ask.
cybersecurity, information security assessments, what are infosec assessments, infosec assessments

Join us and Loraine DeBonis of Ubiquity Compliance Solutions for key takeaways from a panelist at the NBPCA’s Power of Prepaid conference perspective, challenges banks & prepaid program managers are facing regarding the Fed’s Regulation E, improving risk management and more.

You've gone through the 6 steps and best practices for a mid-year third-party risk management progress check, so now what? Listen to learn the next steps to take, how to document your findings and how to improve upon the process as a whole.

Join us and Ed DeMarco, General Counsel and Director of Operational Risk & Regulatory Relations/Communications of the Risk Management Assocation (RMA), for a discussion on vendor risk management challenges & best practices, cybersecurity, regulatory compliance and more.

When you understand why vendor due diligence reviews are necessary, it’s easier to see the increased benefits and make due diligence a priority. Download this vendor management infographic where we'll further explain why.
vendor due diligence, why do we do vendor due diligence, conduct vendor due diligence, how to conduct vendor due diligence

Business continuity planning (BCP) is important to you and your vendors. Listen as we guide you through the appropriate regulatory guidance to follow, what to plan for, what to restore first and how to recover.

Join us and Jim Hussey, Founder of IT-TPRM.com, for a discussion on vendor risk management challenges, why you should place heavier focus on technology or fintech risk, how to engage the first line of defense, advice on meeting OCC lifecycle expectations, best practices and more.

What is a SOC report? It's an audit report performed by a public accounting firm and attests to the existence & effectiveness of the controls put in place to safeguard your data. Listen as we break down 6 important parts.

Learn what is a critical vendor, how to identify your critical vendors, examples of critical vendors and best practices to monitor for proper third-party risk management.
risk assessments, critical vendor, identify critical vendor

Join us and Andrew Lorentz, Attorney at Davis Wright Tremaine LLP. We discuss balancing commercial opportunities with compliance initiatives, importance of community involvement and legal analysis, cybersecurity at exams and outside counsel's view on if the board is properly involved.

How to assess vendor financial risk. Failing to do so can be detrimental to not only your third-party risk management program, but may have direct implications on how you operate your business.
vendor financial risk, assess financial risk, vendor financials, vendor financial risk assessment

The first line of vendor risk management defense has direct interaction on a day-to-day basis with your third-party. Listen to our podcast for 7 best practices for properly engaging the first line of defense.
Items to have prepared, key steps to ensure a successful exam and 14 tips for planning for the day of the examiner's arrival.
exam prep, vendor management exam prep, examination prep, examination preparation

Fourth party risk and liability is often overlooked because there isn't direct relationship with the fourth party vendor. Listen now for the 3 oversight steps to take regarding your fourth party vendors.
When determining your level of oversight on a vendor, you’ll clearly want to determine their criticality and risk level first. Listen to this podcast to help guide you through the process.

Be prepared to comply with the General Data Protection Regulation (GDPR) - it impacts EU and U.S. companies.
GDPR, general data protection regulation, EU regulation
Guide for initial and ongoing due diligence that covers how to do it properly, benefits, items to request, understanding your vendor's regulatory risk impact and more.
vendor due diligence, how to do vendor due diligence, vendor due diligence how to, conduct vendor due diligence

Glen Trudel, Banking and Corporate Attorney at Ballard Spahr, discusses general challenges organizations are facing when it comes to third-party risk and best practices to overcome those hurdles.

A non-elective vendor is one you don't have a direct relationship with, but your third-party does - making them a risk to you and therefore requiring some oversight. Listen to learn the associated responsibilities.
ongoing monitoring, due diligence

Understanding you vendor's classification is a third-party risk management best practice, but what does it mean? This infographic will walk you through the steps to classify your vendors.
vendor management, list creation, vendor rating, risk rating, classify vendors

Join Venminder and James Russell, CPA at Russell Bank Consulting. James discusses third-party risk management changes over the last decade, common third-party risk management issues during examination, how to handle third-party relationships that start to go downhill and more.
audit

An important step to vetting a vendor is onboarding. Learn best practices, how to streamline a vendor vetting process and more.
vendor onboarding, how to onboard a vendor, onboarding a vendor, how to onboard vendors
An important step to vetting a vendor is onboarding. Learn best practices, how to streamline a vendor vetting process and more.
onboarding, onboarding new vendors, onboarding vendors, vendor onboarding

While the General Data Protection Regulation (GDPR) has a global impact on any company which is collecting, storing, or accessing European resident data. Listen to Third-Party Thursday to learn what you need to know.
regulatory guidance, regulatory compliance

Enterprise Risk Management (ERM) and Third-Party Risk Management (TPRM) are are often used interchangeably, but they are two different functions. ERM is more high level, while TPRM is a smaller subset. Listen to learn more.
Third-party risk management

The types of vendor risk management model frameworks, advantages and disadvantages of each, how to help promote consistency and clarity and how to set up.
vendor management models, differences between vendor management models

Recommendations from a seasoned third-party risk expert for how to determine how many staff members to have on your vendor management team. Follow our three tips in this podcast.

Learn 4 tips when determining who your high risk vendors are, what to do with those high risk vendors and key points of assessing risk.
vendor risk, vendor management, risk look big

Join us and Elizabeth Khalil, Partner of Dykema Gossett PLLC. She discusses how third-party risk has evolved, UDAAP risk, the need for vendor management from fintech companies, how defining responsibilities eliminate gaps, why efficient ongoing monitoring is key and more.
regulatory guidance, compliance, oversight management

Venminder sat down with Suresh Ramakrishnan, SVP of Ascendum Solutions, for an interview on third-party risk management best practices and how outsourcing (if managed correctly) can provide greater efficiencies, reduce your workload and help with cost management.
ROI

Save time, money and other valuable resources by learning mistakes companies make with their vendor contracts. Listen to see how you can avoid some common pitfalls during all phases of the vendor lifecycle.
Tips for fostering a third-party risk mindset within your organization - how to create awareness, important members of your company to involve & who the third-party risk responsibility lies within every organization.

In this podcast, you'll learn how your vendor's approach to the CIA triad of information security impacts you and your customers. Being aware will help you against third-party risk.

What makes a third-party risk management plan successful? Listen to learn 9 best practices and key components of a well-managed third-party risk management plan for you to implement now.

Learn how a well-run complaint management system (cms) can turn an upset customer into your best customer along with five elements to include your vendor management policy on complaint management.

Learn why you need your vendor's SOC audit report, if you need their SOC 1 or SOC 2, scope: Is your product/service covered in this report and more.
vendor soc report, analyze soc report, soc reporting, review vendor soc

Here are daily vendor management regulatory compliance efforts you can implement in order to keep up with third-party risk regulatory reform.
regulatory guidance

Learn the how, when and why of using vendor information security questionnaires for your third-party risk management and how your due diligence process can benefit from it.
information security

When reviewing and negotiating critical vendor contracts, consider many elements. Here's 5 key provisions to give special attention.
vendor management, contract management

Listen to this podcast for what you need to know about UDAAP (Unfair, Deceptive or Abusive Acts or Practices), how they affect your third-party risk management program and items the CFPB is highly critical of.
vendor management, regulatory guidance, regulatory compliance

This podcast covers tips and recommendations for determining due diligence questions to ask your fintech vendors. We'll provide insight into setting the standards that should firmly be expected.

Download this infographic for what you need to know to protect your institution, your best insurance against unexpected problems, fundamental requirements of vendor risk management.
vendor management, vendor risk, risk management, tprm

Go through critical vendor classification and identification with us. Learn standards for identifying your vendors, how to properly identify your scope and 3 questions to ask to determine if a vendor is critical.

Join us as we close out 2017 with this thank you vendor management podcast. And, see what our top 10 most popular videos and podcasts were from our Third Party Thursday series for this year.

The best way to prepare for new regulatory guidance, how to stay in compliance and some commentary on new regulations taking effect in 2018.

Use this handy tool to keep you and your team on track to properly measure, monitor and control risks. Learn what is due diligence, the importance of due diligence & the scope.

Learn about 'bucketing your vendors' - a high level vendor classification system that can help you with third-party oversight, ongoing monitoring and preventing problems down the road. We'll also tell you how to develop buckets of your own.
ongoing monitoring, due diligence
In order to have vendor management control, you must have a firm understanding or knowledge of third-party vendor contracts. Learn the 3 pillars in managing them and other points about mitigating contract risk.
contract management

What to include in your complaint policy and complaint management system to improve vendor management. A well-run system can turn upset customers.

How to classify based on product or service, how to classify based on level of risk and next steps to take after you've classified your vendors.
classifying vendor, vendor classification, what is vendor classification, how to classify a vendor

The best strategy for preparing for an examination is to constantly be ready. Listen to learn 7 items you should have in your examination preparation playbook.

How to identify all your vendors, essential steps of vendor management, prioritizing vendors according to risk level and why fourth parties are important.
what is vendor management, what is third-party risk management, vendor risk management meaning, vendor management definition

Download this infographic for 4 tips to help you avoid an enforcement action, 6 top websites for legal analysis, 2 Q's to ask when reviewing enforcement actions.
regulatory guidance, regulatory compliance, vendor management, enforcement actions

Learn how to get ahead of the game education wise in third-party risk management with these 10 best practices. Staying up to date is a great idea for everyone involved in vendor management.

Learn what regulators & senior gov officials in financial services had to say on creating a culture of compliance, why they strongly recommend it and what this entails.

Who should decide and who should approve, why you should not simply accept a boiler plate contract and taking your new vendor through a risk assessment.
pre contract considerations, vendor vetting, vetting a vendor

Learn what regulators & senior gov officials in financial services had to say on creating a culture of compliance, why they strongly recommend it and what this entails.

Download this infographic for who should decide and who should approve, why you should not simply accept a boiler plate contract and taking your new vendor through a risk assessment.
vendor management best practices, third-party risk best practices, best practices in tprm
Learn what regulators & senior gov officials in financial services had to say on creating a culture of compliance, why they strongly recommend it and what this entails.

Sometimes people feel too comfortable with a well-known vendor. We cover why even vendors with recognizable brand names require thorough due diligence. No one is immune from third-party risk.
Learn what info to include in board reports, the frequency and format, the appropriate materials to provide in your board reporting package with this infographic.
reporting

Learn key takeaways from two OCC Bulletins issued this year on third-party risk management - OCC Bulletins 2017-7 and 2017-21. Is your institution's vendor management program in compliance?
regulatory guidance

What the three lines of defense are, how they guard against undue risk and tips for implementing this strategy at your institution.
three lines of defense, 3 lines of defense strategy

What to include in SLAs, about reviewing SLAs and what you can do if one is broken.
service level agreements, slas, vendor service level agreements

Listen to learn the basics of the third-party risk management framework, including how it relates to enterprise risk management (ERM).

13 best practices for managing contracts that you won't find in the FFIEC handbook, where your contracts should be stored and why SLAs in contracts are so important.
contract management, best practices vendor contract, vendor contract best practices, contract best practices

Learn what your policy should consist of, best practices and tips and 3 common errors to avoid with this infographic.
third-party policy, policy creation, how to create third-party policy, write policies

From a risk standpoint, there are some vendors that you should be managing more actively than others.
vendor scope, managed vendors, vendor monitoring

Let's say you find out one of your third parties is named in an enforcement action, even if it is unrelated to your institution, what do you do? Listen to learn the six necessary steps to take.
regulatory guidance, regulatory compliance
Do you know the difference between a critical and non critical vendor? Learn about defining them for your financial institution. We'll cover why it's important, the business impact, exit strategies and more.
risk assessment, rate risk

In this short vendor management video, you will learn four key points you need to know regarding third-party due diligence and what items your due diligence checklist should contain to keep your institution safe from third-party risk.

Learn what the scope of a vendor's SOC report means and where to find it along with what typical audit periods are and a few questions to ask yourself while reviewing the narrative.

Learn the 7 key things you should do with every new vendor. These steps are essential to the vendor vetting process and determining how much you know about the company with whom are you planning to do business.

In this vendor management video, you will learn where to find the controls section within a vendor SOC report along with what the control objectives and activities are and what to look out for in the findings and exceptions.
How you should prepare for an exam ahead of time, who's responsible and our expert tips for the examiner's arrival.
vendor exam, notice of exam, vendor management exam, prepare for exam

We cover the key questions you need to ask yourself to determine if your vendors are critical. Then, we dive deeper and talk about what you should review on your critical risk vendors.
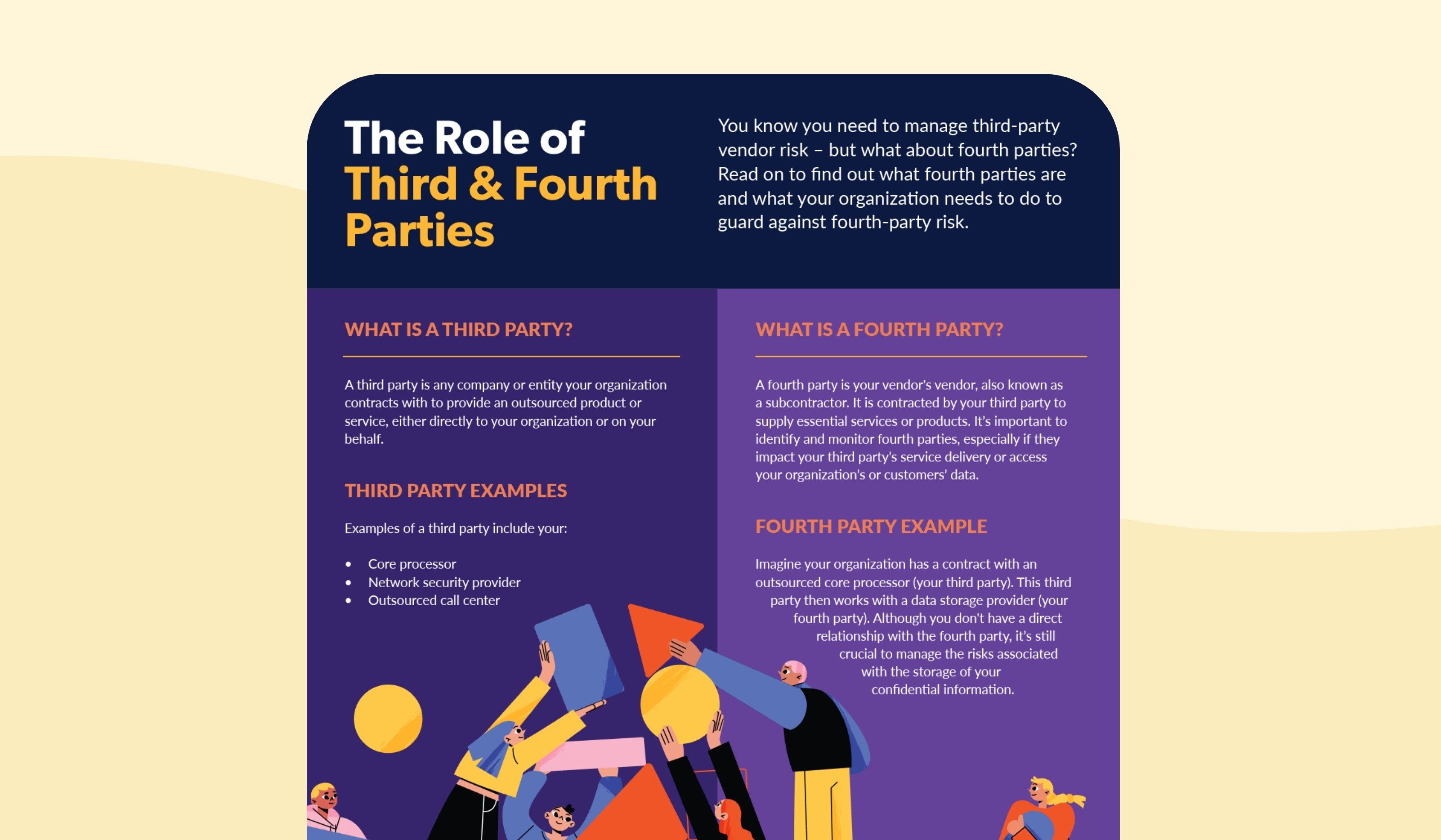
What a fourth-party is vs. a third-party, how to get information on your fourth parties and what to review on your fourth parties.

As of Monday, May 1, SSAE 18 is now in effect. Are you familiar with SSAE 18 yet? Join us now as we talk about SSAE 18 - what it is and how it affects how you do vendor management at your institution. Let's get started.

We’re going to talk through a few key things you need to know about vendor management risk assessments for your organization's third-party risk management program.

Improve your vendor risk management program, what requesting one means, what to do if your vendor won't give those reports to you, another way of obtaining the reports.
due diligence items, vendor manager due diligence, vendor manager

We’re going to talk through the 10 main steps you need to take to create your proper vendor list for your third-party risk management program at your institution. Let's get started.
The consequences of making these mistakes and an opportunity to visit your contract process and ensure that you have firm standards in place.
vendor contract management, contract management mistakes, vendor contracts

10 errors we commonly see in vendor management programs - check your program now to find out if you have any gaps that need fixing.
You may have heard the term “three lines of defense”. But, what is a three lines of defense strategy? We'll go through those three lines of defense you have for vendor management at your financial institution.

This assessment identifies how information is being secured to see risks present by engaging in business with the vendor.

Prepping for an audit is stressful, especially if you're scrambling last minute to finish vendor management tasks. In this 90-second podcast, learn 8 steps to help you prepare in advance.
examination

In this 90-second podcast, we cover the three most important reasons why you need to keep third-party risk workflows separate from other business processes.

How to work with overseas vendors and give them special attention, whether they're a third-party or fourth-party.

We'll discuss fundamental best practices of third-party risk management that you need to implement such as education, tailored ongoing monitoring, outsourcing and not cutting corners.

Customer complaints are a fact of life in the social media world we live in today. See why you need to monitor your vendor's complaints as a critical part of third party risk management.

7 vendor management nightmares and ensure you take the necessary steps to avoid.
vendor management risk, vendor management nightmares, vendor management next steps

Venminder was honored to be joined by David Stevens, President and CEO of the Mortgage Bankers Association (MBA). Listen to this interview for discussions on data security, cybersecurity, lessons learned from the housing crisis, the CFPB relation to regulatory compliance and much more.
regulatory guidance

This Venminder interview drills down into a specific vendor type - the appraisal management company (AMC) and appraisal management software. With Shane Martin, EVP of InHouseUSA, we discuss the specific areas of third-party risk to pay attention to when using an AMC as fourth-party vendor.
regtech

You should be familiar with Appendix J and Appendix E of the FFIEC guidance. We will go over what each of them are, what they mean and how your teams can stay informed on new vendor management guidance and regulations.
regulatory compliance, guidance

Learn 7 key things you should do with every new vendor. These steps are essential to the vendor vetting process and determining how much you know about the company with whom are you planning to do business.
Our in-house third-party risk experts can help determine if your vendor's operational and regulatory compliance is satisfactory.
regulatory compliance

Items to collect on all vendors, what to collect for higher risk or more critical vendors, and suggestions when you need to fill due diligence gaps.
product documentation formula, vendor risk formula
It’s easy to get so deep in the weeds of your vendor management program that you make some pretty basic errors. Sometimes you need to take a step back and evaluate. Here are some of the ones that we see most often.

4 key elements in every disaster recovery plan and why you should care about your third parties' disaster recovery preparedness.
disaster recovery, vendor disaster recovery, disaster recovery planning, vendor management, DR, TPRM

Considerations when you outsource to a contract underwriter, 3 tips in vendor oversight, Q's to consider when assessing contract underwriter risk.
mortgage underwriter, contract mortgage underwriter, contract management

How to mitigate reputation risk, the impact a vendor can have on your reputation, which vendors pose a reputational risk and 5 tactics to manage third party reputational risk.

We often get asked, "Is there a difference between an ERM and VM?" The answer is “YES” – they are different, but there are some areas of overlap as well. Learn about what some of the differences are.
Our analysis of OCC 2017-7 to learn key points to know about Bulletin 2017-7 and actions required to comply.
occ bulletin 2017-7, occ bulletins, guide to occ bulletin 2017-7

What you need to know about SSAE 18, the difference between SSAE 16 and SSAE 18 and some key updates to SOC 1's.

Do you know if they have appropriate measures in place and a plan of how to handle business impacting events with you?

7 signs to look for when reviewing your vendor list to see if any of them are under-performing and steps to protect you if you spot one.
Contract management best practices, summarizing key guidance expectations from reglators and common issues and consequences.
vendor contracts, contract managements, vendor contract management, third-party contract, third-party contract management

The Procedures must be very detailed, often right down to the prescriptive steps of what screen to look at, what field to examine, what step to take next, etc.

So you're asking yourself right now, "What is a fourth party? I've just gotten my head around the whole concept of having third parties. And why are they important to my financial institution's vendor management program?" Let's discuss.
When you’re examined, the Program will absolutely positively be essential. Examiners will look for consistency in form and in content.

When a third-party company doesn't provide financial documents we tend to think there's nothing we can do. But actually, there is and we'll show you that alternate path in this video.

Your vendor management Policy is the playbook that auditors and examiners will expect you to follow. Get the Policy right and it will provide your financial institution all the right protection in weathering the storm.

Learn the 3 key points to review in service organization control reports, SOC reports for short, as you begin assessing your vendor's environment. Meet examiner requests and gain strategic business advantages.

Here's your starting point of our 4-part series that covers the 3 primary components essential to building an exam proof vendor management operation at your financial institution.

You have to do a lot for your third party risk management now... but why? We'll go through a few reasons for the increased third-party risk management regulation and concern.

You report the vendor's financial health to senior management and board. What happens when the financial health is poor? We will go over the domino effect, the issue in the industry and what you can do about it.

Ensuring your critical vendors can survive in disaster helps ensure your financial institution can also survive. Learn what Business Continuity & Disaster Recovery plans are & how our team reviews them.

To help you and your team avoid any misunderstandings, we've put together a list of 10 most common assumptions we've seen in the vendor management process.

To help you and your team, we've put together a simple infographic on 7 of the most common dangerous potholes that we have seen.

To join in the fun of St. Patricks Day every year, we've put together a simple infographic on the basic principles of a successful vendor management program.

The FFIEC released a Cybersecurity Assessment Tool. We'll go over in depth the benefits of it and why your financial institution should use it for your vendor management.

Does your due diligence process include assessing your vendor's cybersecurity posture? Have you identified the risks and applied controls to mitigate the risk? And if something goes wrong, what happens next?
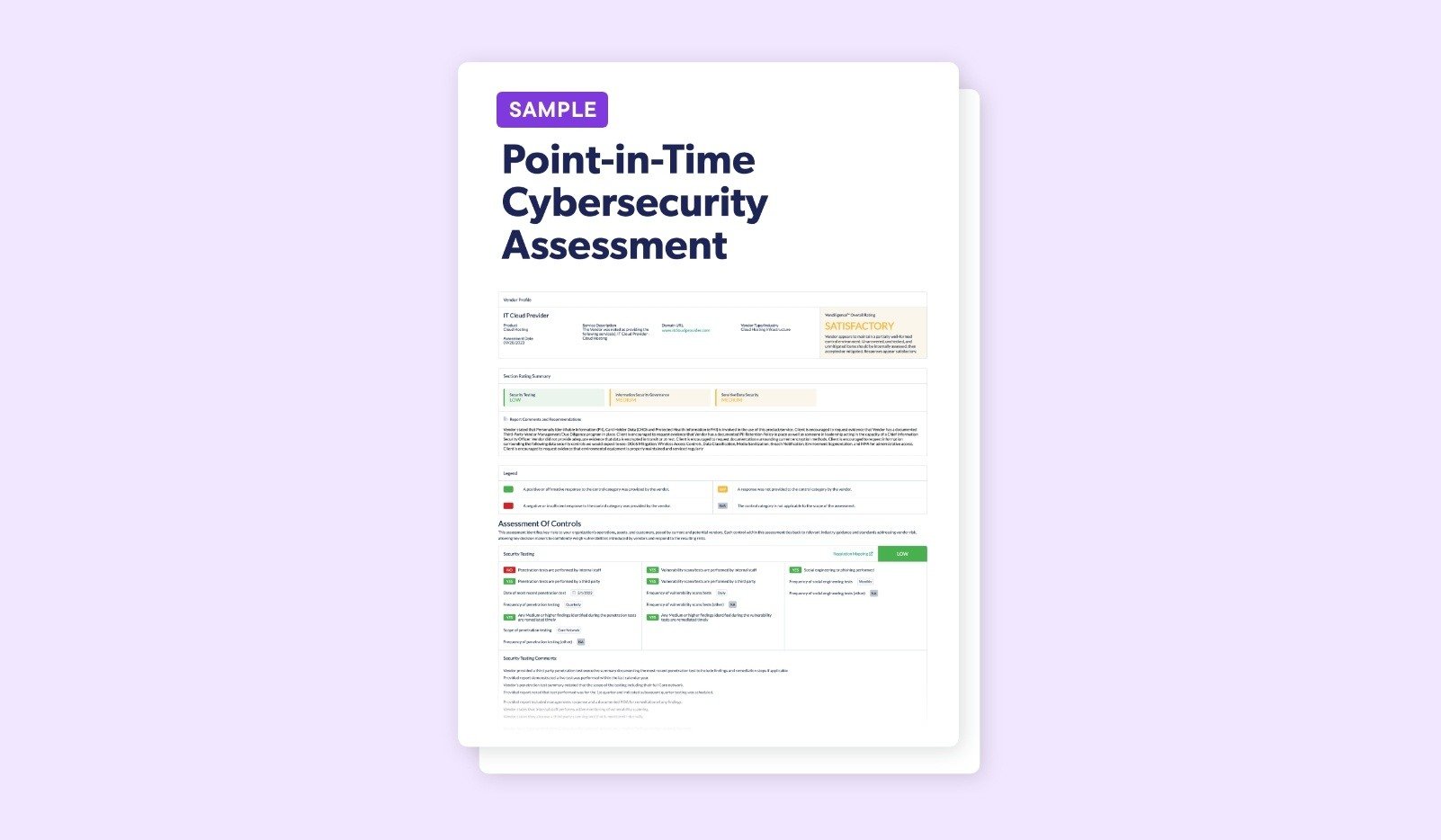
Download our sample Point-In-Time Cybersecurity Analysis and feel free to use it as a guide for doing your own assessments or contact us if outsourcing this type of work is right for you.
information security

Even though each vendor agreement includes different contractual terms, 5 security and confidentiality provisions should always be addressed. Let's go through them.
cybersecurity, information security

Love is in the air this Valentine's Day. But "love" may not be the word you would pick to describe the relationship you have with all of your vendors.

So, what are the types of service organization control (SOC) reports and which type of SOC report did your vendors have performed? To help keep track, we'll cover all 5 of them in this podcast.
cybersercurity, information security

The Cloud has many benefits, but there are risks you need to consider. Protecting your organization's data is ultimately your responsibility so you should know how your vendor safeguards it.
cybersecurity, information security

We firmly believe that if you follow a few basic steps before you enter a contract, you're unlikely to ever need to pull that contract out again during the term of the relationship.
contract management, contract negotiation
Our comprehensive summary report detail each provision and notate those that are covered, and just as importantly, those that are missing and need to be addressed in the next revision.
contract management, contract negotiation
In this video we cover the evolution of third-party risk management and the regulatory expectations on financial institutions. This will be helpful to know as you expand your third-party risk knowledge.
regulatory compliance, guidance

Various components of vendor risk feed in to your ERM strategy and considerations. Learn steps and tips on how to properly integrate third-party risk management in your enterprise risk management program.

Learn what Complimentary User Entity Controls are, how they're related to SOC reports, what you do with them, why they're important and more.
cybersecurity, information security
Download our sample vendor business continuity plan review and feel free to use it as a guide for doing your own or contact us if outsourcing this type of work is right for you.
bcp

It is essential for the future success of your third-party risk management program to continue to make necessary updates. These 6 steps and best practices will help get you started.
due diligence, ongoing monitoring, oversight management
Check out our latest third-party risk blog posts that you may also find helpful.
May 21, 2026 by Alesha Briley, CRCM
Here are the latest updates on Section 1071 implementation and broader Consumer Protection Bureau (CFPB) oversight.
...
May 21, 2026 by Rebecca Tetreau
The regulatory landscape for financial organizations is shifting. Agencies are rescinding guidance, rewriting rules,...
May 19, 2026 by Michael Berman
Compliance management is expensive to oversee, but it’s even more expensive to get wrong. An enforcement action can...
Be the first to know when we add new infographics, blog posts, and more.